搜索到
154
篇与
的结果
-
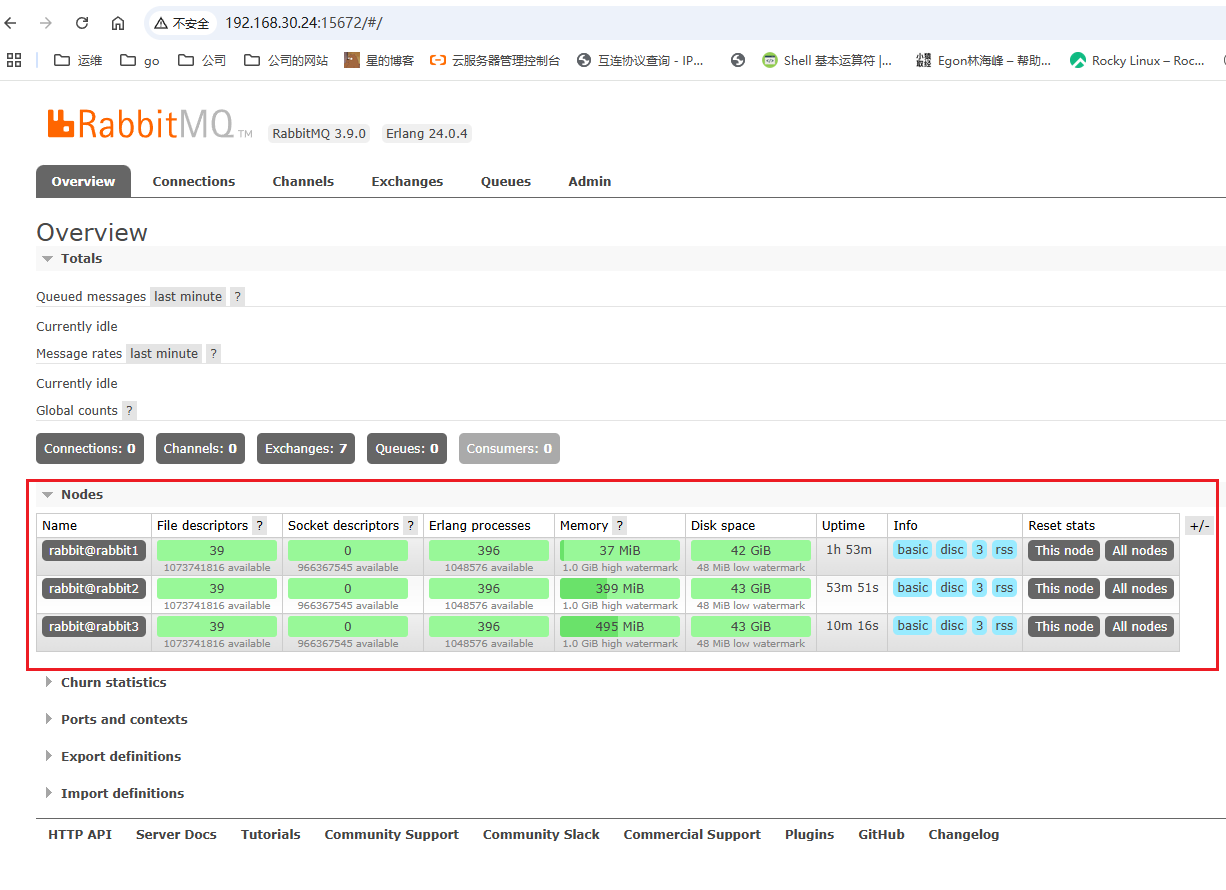
 rabbitmq安装 一、配置docker加速cat > /etc/docker/daemon.json <<EOF { "registry-mirrors": ["https://15.164.211.114:6443"], "insecure-registries": ["15.164.211.114:6443"], "exec-opts": ["native.cgroupdriver=systemd"] } EOF# 重启Docker服务 systemctl daemon-reload && systemctl restart docker二、准备配置文件和集群规划hostnamectl set-hostname 主机名[root@rabbit1 mq]# cat /etc/hosts 127.0.0.1 localhost localhost.localdomain localhost4 localhost4.localdomain4 ::1 localhost localhost.localdomain localhost6 localhost6.localdomain6 192.168.30.24 rabbit1 192.168.30.25 rabbit2 192.168.30.26 rabbit3#关闭防火墙 sudo systemctl stop firewalld sudo systemctl disable firewalld#主节点 [root@rabbit1 mq]# cat docker-compose.yml version: '3.3' services: rabbitmq: image: rabbitmq:3.9.0-management container_name: rabbitmq restart: always privileged: true network_mode: "host" hostname: rabbit1 environment: RABBITMQ_NODENAME: "rabbit@rabbit1" volumes: - ./data:/var/lib/rabbitmq - ./logs:/var/log/rabbitmq - ./config/rabbitmq.conf:/etc/rabbitmq/rabbitmq.conf - ./config/definitions.json:/etc/rabbitmq/definitions.json - ./config/.erlang.cookie:/var/lib/rabbitmq/.erlang.cookie - ./custom_plugins:/plugins/custom [root@rabbit1 mq]# cat ./config/rabbitmq.conf # Config for rabbit1 listeners.tcp.default = 5672 management.tcp.port = 15672 management.tcp.ip = 0.0.0.0 loopback_users.guest = false log.file.level = info [root@rabbit1 mq]# cat ./config/definitions.json { "users": [{ "name": "admin", "password": "7UKMq2UWj4PmTWd6zjMX", "tags": "administrator" }], "vhosts": [{ "name": "/" }], "permissions": [{ "user": "admin", "vhost": "/", "configure": ".*", "write": ".*", "read": ".*" }] } echo "MY_RABBITMQ_CLUSTER_SECRET" | tr -d '\n' > /root/mq/config/.erlang.cookie chmod 600 /root/mq/config/.erlang.cookie#准备好插件 [root@rabbit1 mq]# ls config custom_plugins data docker-compose.yml logs rabbitmq.tar [root@rabbit1 mq]# ls custom_plugins/ rabbitmq_delayed_message_exchange-3.9.0.ez三、启动#停止 docker-compose down #启动 后面加-d后台启动 docker-compose up #清理缓存慎重 docker system prune -f#启动后要把logs文件夹给权限 chmod -R +777 ./logs/#插件安装 [root@rabbit3 mq]# docker exec -it rabbitmq bash root@rabbit3:/# cp /plugins/custom/rabbitmq_delayed_message_exchange-3.9.0.ez /opt/rabbitmq/plugins/ root@rabbit3:/# rabbitmq-plugins enable rabbitmq_delayed_message_exchange Enabling plugins on node rabbit@rabbit3: rabbitmq_delayed_message_exchange The following plugins have been configured: rabbitmq_delayed_message_exchange rabbitmq_management rabbitmq_management_agent rabbitmq_prometheus rabbitmq_web_dispatch Applying plugin configuration to rabbit@rabbit3... The following plugins have been enabled: rabbitmq_delayed_message_exchange started 1 plugins.四、加入集群从节点加入集群需要改配置文件,然后执行下面加入命令 [root@rabbit3 mq]# cat docker-compose.yml version: '3.3' services: rabbitmq: image: rabbitmq:3.9.0-management container_name: rabbitmq restart: always privileged: true network_mode: "host" hostname: rabbit3 #这里 environment: RABBITMQ_NODENAME: "rabbit@rabbit3" #这里 volumes: - ./data:/var/lib/rabbitmq - ./logs:/var/log/rabbitmq - ./config/rabbitmq.conf:/etc/rabbitmq/rabbitmq.conf - ./config/definitions.json:/etc/rabbitmq/definitions.json - ./config/.erlang.cookie:/var/lib/rabbitmq/.erlang.cookie #- ./plugins:/plugins - ./custom_plugins:/plugins/custom[root@rabbit3 mq]# docker exec rabbitmq rabbitmqctl import_definitions /etc/rabbitmq/definitions.json Importing definitions in JSON from a file at "/etc/rabbitmq/definitions.json" ... Successfully started definition import. This process is asynchronous and can take some time. [root@rabbit3 mq]# docker restart rabbitmq rabbitmq [root@rabbit3 mq]# docker exec -it rabbitmq bash root@rabbit3:/# rabbitmqctl stop_app Stopping rabbit application on node rabbit@rabbit3 ... root@rabbit3:/# rabbitmqctl join_cluster rabbit@rabbit1 Clustering node rabbit@rabbit3 with rabbit@rabbit1 root@rabbit3:/# rabbitmqctl start_app Starting node rabbit@rabbit3 ... root@rabbit3:/#
rabbitmq安装 一、配置docker加速cat > /etc/docker/daemon.json <<EOF { "registry-mirrors": ["https://15.164.211.114:6443"], "insecure-registries": ["15.164.211.114:6443"], "exec-opts": ["native.cgroupdriver=systemd"] } EOF# 重启Docker服务 systemctl daemon-reload && systemctl restart docker二、准备配置文件和集群规划hostnamectl set-hostname 主机名[root@rabbit1 mq]# cat /etc/hosts 127.0.0.1 localhost localhost.localdomain localhost4 localhost4.localdomain4 ::1 localhost localhost.localdomain localhost6 localhost6.localdomain6 192.168.30.24 rabbit1 192.168.30.25 rabbit2 192.168.30.26 rabbit3#关闭防火墙 sudo systemctl stop firewalld sudo systemctl disable firewalld#主节点 [root@rabbit1 mq]# cat docker-compose.yml version: '3.3' services: rabbitmq: image: rabbitmq:3.9.0-management container_name: rabbitmq restart: always privileged: true network_mode: "host" hostname: rabbit1 environment: RABBITMQ_NODENAME: "rabbit@rabbit1" volumes: - ./data:/var/lib/rabbitmq - ./logs:/var/log/rabbitmq - ./config/rabbitmq.conf:/etc/rabbitmq/rabbitmq.conf - ./config/definitions.json:/etc/rabbitmq/definitions.json - ./config/.erlang.cookie:/var/lib/rabbitmq/.erlang.cookie - ./custom_plugins:/plugins/custom [root@rabbit1 mq]# cat ./config/rabbitmq.conf # Config for rabbit1 listeners.tcp.default = 5672 management.tcp.port = 15672 management.tcp.ip = 0.0.0.0 loopback_users.guest = false log.file.level = info [root@rabbit1 mq]# cat ./config/definitions.json { "users": [{ "name": "admin", "password": "7UKMq2UWj4PmTWd6zjMX", "tags": "administrator" }], "vhosts": [{ "name": "/" }], "permissions": [{ "user": "admin", "vhost": "/", "configure": ".*", "write": ".*", "read": ".*" }] } echo "MY_RABBITMQ_CLUSTER_SECRET" | tr -d '\n' > /root/mq/config/.erlang.cookie chmod 600 /root/mq/config/.erlang.cookie#准备好插件 [root@rabbit1 mq]# ls config custom_plugins data docker-compose.yml logs rabbitmq.tar [root@rabbit1 mq]# ls custom_plugins/ rabbitmq_delayed_message_exchange-3.9.0.ez三、启动#停止 docker-compose down #启动 后面加-d后台启动 docker-compose up #清理缓存慎重 docker system prune -f#启动后要把logs文件夹给权限 chmod -R +777 ./logs/#插件安装 [root@rabbit3 mq]# docker exec -it rabbitmq bash root@rabbit3:/# cp /plugins/custom/rabbitmq_delayed_message_exchange-3.9.0.ez /opt/rabbitmq/plugins/ root@rabbit3:/# rabbitmq-plugins enable rabbitmq_delayed_message_exchange Enabling plugins on node rabbit@rabbit3: rabbitmq_delayed_message_exchange The following plugins have been configured: rabbitmq_delayed_message_exchange rabbitmq_management rabbitmq_management_agent rabbitmq_prometheus rabbitmq_web_dispatch Applying plugin configuration to rabbit@rabbit3... The following plugins have been enabled: rabbitmq_delayed_message_exchange started 1 plugins.四、加入集群从节点加入集群需要改配置文件,然后执行下面加入命令 [root@rabbit3 mq]# cat docker-compose.yml version: '3.3' services: rabbitmq: image: rabbitmq:3.9.0-management container_name: rabbitmq restart: always privileged: true network_mode: "host" hostname: rabbit3 #这里 environment: RABBITMQ_NODENAME: "rabbit@rabbit3" #这里 volumes: - ./data:/var/lib/rabbitmq - ./logs:/var/log/rabbitmq - ./config/rabbitmq.conf:/etc/rabbitmq/rabbitmq.conf - ./config/definitions.json:/etc/rabbitmq/definitions.json - ./config/.erlang.cookie:/var/lib/rabbitmq/.erlang.cookie #- ./plugins:/plugins - ./custom_plugins:/plugins/custom[root@rabbit3 mq]# docker exec rabbitmq rabbitmqctl import_definitions /etc/rabbitmq/definitions.json Importing definitions in JSON from a file at "/etc/rabbitmq/definitions.json" ... Successfully started definition import. This process is asynchronous and can take some time. [root@rabbit3 mq]# docker restart rabbitmq rabbitmq [root@rabbit3 mq]# docker exec -it rabbitmq bash root@rabbit3:/# rabbitmqctl stop_app Stopping rabbit application on node rabbit@rabbit3 ... root@rabbit3:/# rabbitmqctl join_cluster rabbit@rabbit1 Clustering node rabbit@rabbit3 with rabbit@rabbit1 root@rabbit3:/# rabbitmqctl start_app Starting node rabbit@rabbit3 ... root@rabbit3:/# -
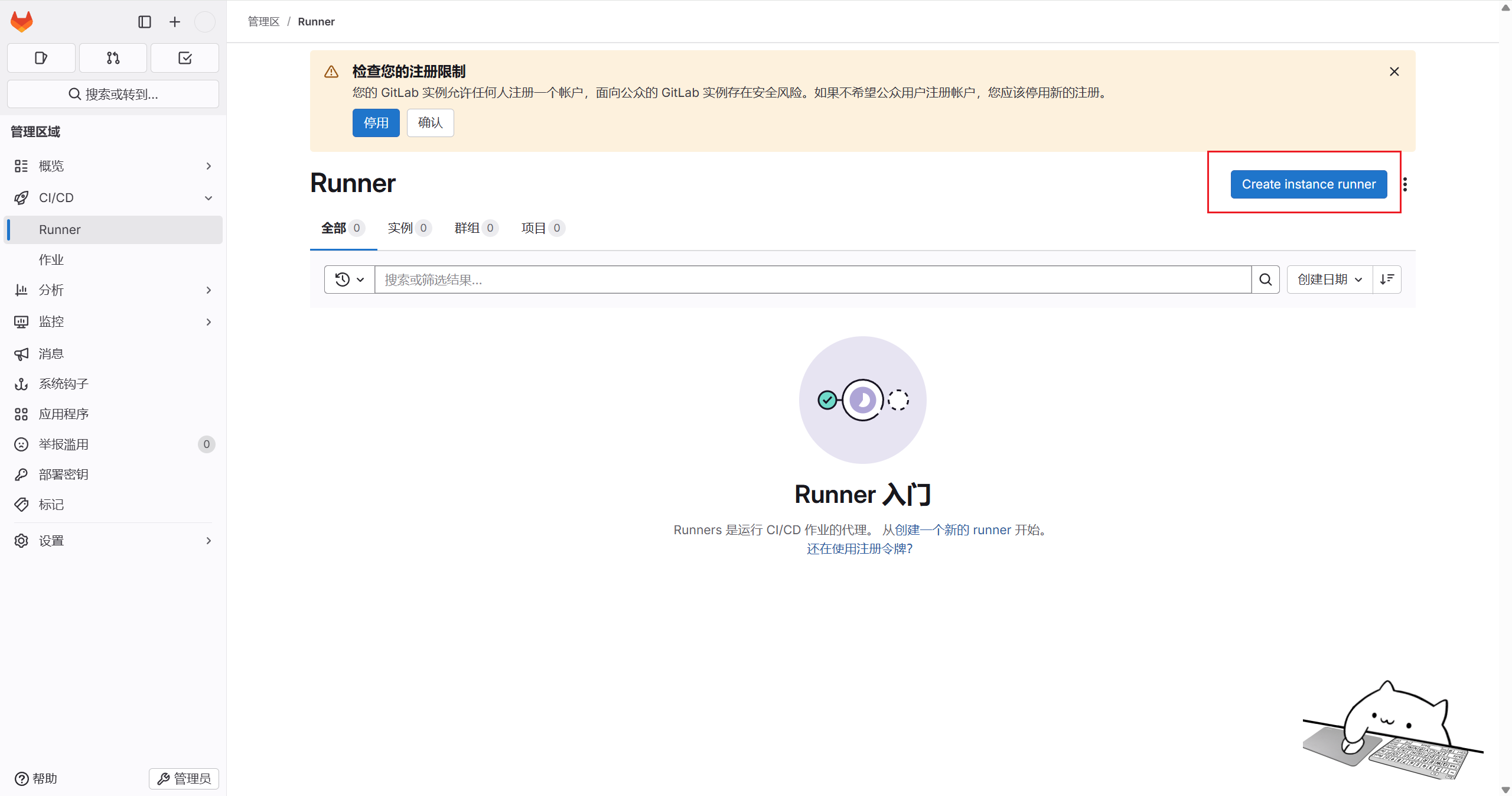
 runner注册 一、gitlab runner类型shared:运行整个平台项目的作业(gitlab) group:运行特定group下的所有项目的作业(group) specific:运行指定的项目作业(project)二、创建不同类型的runner 2.1shared类型依次点击主页——>管理中心——>CI/CD——>Runner——>新建实例runner#按命令提示输入之后 回车 然后 按自己安装runner的模式 shell还是docker root@k8s-02:~# gitlab-runner register --url http://192.168.30.181 --token glrt-KXvcjZNVMVtCustGF-O3Z286MQp0OjEKdToxCw.01.121vlf8dr Runtime platform arch=amd64 os=linux pid=23285 revision=cc489270 version=18.2.1 Running in system-mode. Enter the GitLab instance URL (for example, https://gitlab.com/): [http://192.168.30.181]: Verifying runner... is valid correlation_id=01K2CM5N1H5TAGE79WMJ9CMDQN runner=KXvcjZNVM Enter a name for the runner. This is stored only in the local config.toml file: [k8s-02]: Enter an executor: docker-windows, docker-autoscaler, instance, shell, ssh, parallels, docker, docker+machine, kubernetes, custom, virtualbox: ERROR: Invalid executor specified Enter an executor: kubernetes, custom, virtualbox, docker-windows, docker-autoscaler, instance, shell, ssh, parallels, docker, docker+machine: ERROR: Invalid executor specified Enter an executor: custom, virtualbox, docker-windows, docker-autoscaler, instance, shell, ssh, parallels, docker, docker+machine, kubernetes: ERROR: Invalid executor specified Enter an executor: custom, virtualbox, docker-windows, docker-autoscaler, instance, shell, ssh, parallels, docker, docker+machine, kubernetes: ERROR: Invalid executor specified Enter an executor: instance, shell, ssh, parallels, docker, docker+machine, kubernetes, custom, virtualbox, docker-windows, docker-autoscaler: ERROR: Invalid executor specified Enter an executor: parallels, docker, docker+machine, kubernetes, custom, virtualbox, docker-windows, docker-autoscaler, instance, shell, ssh: shell Runner registered successfully. Feel free to start it, but if it's running already the config should be automatically reloaded! Configuration (with the authentication token) was saved in "/etc/gitlab-runner/config.toml" 2.2group类型依次点击主页——>群组——>指定组——>设置——>构建——>runner——>新建群组runner
runner注册 一、gitlab runner类型shared:运行整个平台项目的作业(gitlab) group:运行特定group下的所有项目的作业(group) specific:运行指定的项目作业(project)二、创建不同类型的runner 2.1shared类型依次点击主页——>管理中心——>CI/CD——>Runner——>新建实例runner#按命令提示输入之后 回车 然后 按自己安装runner的模式 shell还是docker root@k8s-02:~# gitlab-runner register --url http://192.168.30.181 --token glrt-KXvcjZNVMVtCustGF-O3Z286MQp0OjEKdToxCw.01.121vlf8dr Runtime platform arch=amd64 os=linux pid=23285 revision=cc489270 version=18.2.1 Running in system-mode. Enter the GitLab instance URL (for example, https://gitlab.com/): [http://192.168.30.181]: Verifying runner... is valid correlation_id=01K2CM5N1H5TAGE79WMJ9CMDQN runner=KXvcjZNVM Enter a name for the runner. This is stored only in the local config.toml file: [k8s-02]: Enter an executor: docker-windows, docker-autoscaler, instance, shell, ssh, parallels, docker, docker+machine, kubernetes, custom, virtualbox: ERROR: Invalid executor specified Enter an executor: kubernetes, custom, virtualbox, docker-windows, docker-autoscaler, instance, shell, ssh, parallels, docker, docker+machine: ERROR: Invalid executor specified Enter an executor: custom, virtualbox, docker-windows, docker-autoscaler, instance, shell, ssh, parallels, docker, docker+machine, kubernetes: ERROR: Invalid executor specified Enter an executor: custom, virtualbox, docker-windows, docker-autoscaler, instance, shell, ssh, parallels, docker, docker+machine, kubernetes: ERROR: Invalid executor specified Enter an executor: instance, shell, ssh, parallels, docker, docker+machine, kubernetes, custom, virtualbox, docker-windows, docker-autoscaler: ERROR: Invalid executor specified Enter an executor: parallels, docker, docker+machine, kubernetes, custom, virtualbox, docker-windows, docker-autoscaler, instance, shell, ssh: shell Runner registered successfully. Feel free to start it, but if it's running already the config should be automatically reloaded! Configuration (with the authentication token) was saved in "/etc/gitlab-runner/config.toml" 2.2group类型依次点击主页——>群组——>指定组——>设置——>构建——>runner——>新建群组runner -
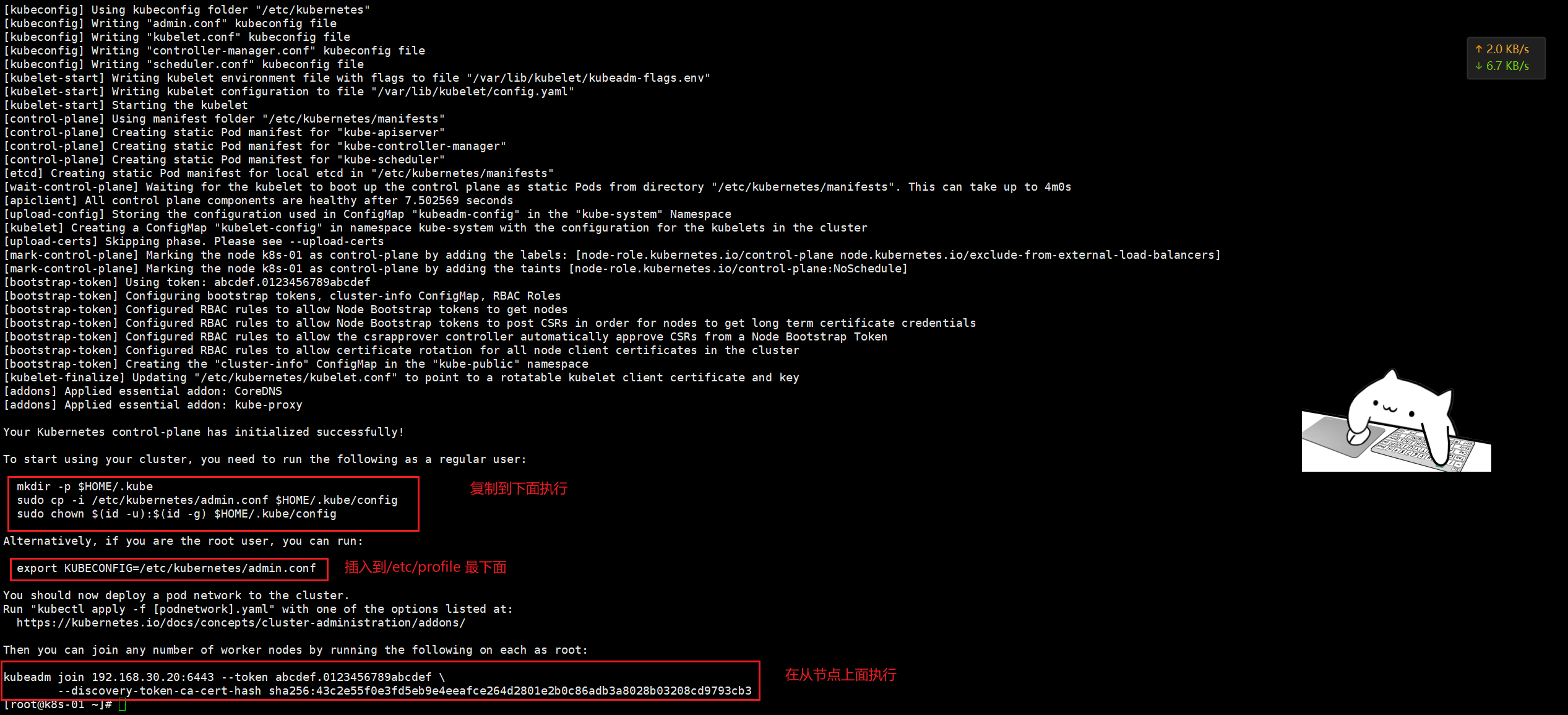
 Rocky Linux 9.3 安装k8s-docker安装 一、固定IP地址#配置 sudo nmcli connection modify ens160 \ ipv4.method manual \ ipv4.addresses 192.168.30.20/24 \ ipv4.gateway 192.168.30.2 \ ipv4.dns "8.8.8.8,8.8.4.4" #更新配置 sudo nmcli connection down ens160 && sudo nmcli connection up ens160二、配置yum源 2.1备份现有仓库配置文件#sudo mkdir /etc/yum.repos.d/backup #sudo mv /etc/yum.repos.d/*.repo /etc/yum.repos.d/backup/ 直接执行下面的2.2修改仓库配置文件# 使用阿里云推荐的配置方法 sudo sed -e 's!^mirrorlist=!#mirrorlist=!g' \ -e 's!^#baseurl=http://dl.rockylinux.org/$contentdir!baseurl=https://mirrors.aliyun.com/rockylinux!g' \ -i /etc/yum.repos.d/Rocky-*.repo2.3清理并重建缓存sudo dnf clean all sudo dnf makecache2.4测试更新sudo dnf update -y三、准备工作 3.1修改主机名hostnamectl set-hostname k8s-01 hostnamectl set-hostname k8s-02 hostnamectl set-hostname k8s-033.2关闭一些服务# 1、关闭selinux sed -i 's#enforcing#disabled#g' /etc/selinux/config setenforce 0 # 2、禁用防火墙,网络管理,邮箱 systemctl disable --now firewalld NetworkManager postfix # 3、关闭swap分区 swapoff -a # 注释swap分区 cp /etc/fstab /etc/fstab_bak sed -i '/swap/d' /etc/fstab3.3sshd服务优化(可以不做)# 1、加速访问 sed -ri 's@^#UseDNS yes@UseDNS no@g' /etc/ssh/sshd_config sed -ri 's#^GSSAPIAuthentication yes#GSSAPIAuthentication no#g' /etc/ssh/sshd_config grep ^UseDNS /etc/ssh/sshd_config grep ^GSSAPIAuthentication /etc/ssh/sshd_config systemctl restart sshd # 2、密钥登录(主机点做):为了让后续一些远程拷贝操作更方便 ssh-keygen ssh-copy-id -i root@k8s-01 ssh-copy-id -i root@k8s-02 ssh-copy-id -i root@k8s-03 #连接测试 [root@m01 ~]# ssh 172.16.1.7 Last login: Tue Nov 24 09:02:26 2020 from 10.0.0.1 [root@web01 ~]#3.4增大文件标识符数量(退出当前会话立即生效)cat > /etc/security/limits.d/k8s.conf <<EOF * soft nofile 65535 * hard nofile 131070 EOF ulimit -Sn ulimit -Hn3.5所有节点配置模块自动加载,此步骤不做的话(kubeadm init时会直接失败)modprobe br_netfilter modprobe ip_conntrack cat >>/etc/rc.sysinit<<EOF #!/bin/bash for file in /etc/sysconfig/modules/*.modules ; do [ -x $file ] && $file done EOF echo "modprobe br_netfilter" >/etc/sysconfig/modules/br_netfilter.modules echo "modprobe ip_conntrack" >/etc/sysconfig/modules/ip_conntrack.modules chmod 755 /etc/sysconfig/modules/br_netfilter.modules chmod 755 /etc/sysconfig/modules/ip_conntrack.modules lsmod | grep br_netfilter3.6同步集群时间# =====================》chrony服务端:服务端我们可以自己搭建,也可以直接用公网上的时间服务器,所以是否部署服务端看你自己 # 1、安装 dnf -y install chrony # 2、修改配置文件 mv /etc/chrony.conf /etc/chrony.conf.bak cat > /etc/chrony.conf << EOF server ntp1.aliyun.com iburst minpoll 4 maxpoll 10 server ntp2.aliyun.com iburst minpoll 4 maxpoll 10 server ntp3.aliyun.com iburst minpoll 4 maxpoll 10 server ntp4.aliyun.com iburst minpoll 4 maxpoll 10 server ntp5.aliyun.com iburst minpoll 4 maxpoll 10 server ntp6.aliyun.com iburst minpoll 4 maxpoll 10 server ntp7.aliyun.com iburst minpoll 4 maxpoll 10 driftfile /var/lib/chrony/drift makestep 10 3 rtcsync allow 0.0.0.0/0 local stratum 10 keyfile /etc/chrony.keys logdir /var/log/chrony stratumweight 0.05 noclientlog logchange 0.5 EOF # 4、启动chronyd服务 systemctl restart chronyd.service # 最好重启,这样无论原来是否启动都可以重新加载配置 systemctl enable chronyd.service systemctl status chronyd.service # =====================》chrony客户端:在需要与外部同步时间的机器上安装,启动后会自动与你指定的服务端同步时间 # 下述步骤一次性粘贴到每个客户端执行即可 # 1、安装chrony dnf -y install chrony # 2、需改客户端配置文件 mv /etc/chrony.conf /etc/chrony.conf.bak cat > /etc/chrony.conf << EOF server 192.168.30.20 iburst driftfile /var/lib/chrony/drift makestep 10 3 rtcsync local stratum 10 keyfile /etc/chrony.key logdir /var/log/chrony stratumweight 0.05 noclientlog logchange 0.5 EOF # 3、启动chronyd systemctl restart chronyd.service systemctl enable chronyd.service systemctl status chronyd.service # 4、验证 chronyc sources -v3.7安装常用软件dnf -y install expect wget jq psmisc vim net-tools telnet yum-utils device-mapper-persistent-data lvm2 git ntpdate chrony bind-utils rsync unzip git3.8查看内核版本要4.4+[root@localhost ~]# grubby --default-kernel /boot/vmlinuz-5.14.0-570.30.1.el9_6.x86_643.8节点安装IPVS# 1、安装ipvsadm等相关工具 dnf -y install ipvsadm ipset sysstat conntrack libseccomp # 2、配置加载 cat > /etc/sysconfig/modules/ipvs.modules <<"EOF" #!/bin/bash ipvs_modules="ip_vs ip_vs_lc ip_vs_wlc ip_vs_rr ip_vs_wrr ip_vs_lblc ip_vs_lblcr ip_vs_dh ip_vs_sh ip_vs_fo ip_vs_nq ip_vs_sed ip_vs_ftp nf_conntrack" for kernel_module in ${ipvs_modules}; do /sbin/modinfo -F filename ${kernel_module} > /dev/null 2>&1 if [ $? -eq 0 ]; then /sbin/modprobe ${kernel_module} fi done EOF chmod 755 /etc/sysconfig/modules/ipvs.modules && bash /etc/sysconfig/modules/ipvs.modules && lsmod | grep ip_vs3.9机器修改内核参数cat > /etc/sysctl.d/k8s.conf << EOF net.ipv4.ip_forward = 1 net.bridge.bridge-nf-call-iptables = 1 net.bridge.bridge-nf-call-ip6tables = 1 fs.may_detach_mounts = 1 vm.overcommit_memory=1 vm.panic_on_oom=0 fs.inotify.max_user_watches=89100 fs.file-max=52706963 fs.nr_open=52706963 net.ipv4.tcp_keepalive_time = 600 net.ipv4.tcp.keepaliv.probes = 3 net.ipv4.tcp_keepalive_intvl = 15 net.ipv4.tcp.max_tw_buckets = 36000 net.ipv4.tcp_tw_reuse = 1 net.ipv4.tcp.max_orphans = 327680 net.ipv4.tcp_orphan_retries = 3 net.ipv4.tcp_syncookies = 1 net.ipv4.tcp_max_syn_backlog = 16384 net.ipv4.ip_conntrack_max = 65536 net.ipv4.tcp_max_syn_backlog = 16384 net.ipv4.top_timestamps = 0 net.core.somaxconn = 16384 EOF # 立即生效 sysctl --system四、安装containerd(所有k8s节点都要做) 自Kubernetes1.24以后,K8S就不再原生支持docker了我们都知道containerd来自于docker,后被docker捐献给了云原生计算基金会(我们安装docker当然会一并安装上containerd)安装方法:centos的libseccomp的版本为2.3.1,不满足containerd的需求,需要下载2.4以上的版本即可,我这里部署2.5.1版本。 rpm -e libseccomp-2.5.1-1.el8.x86_64 --nodeps rpm -ivh libseccomp-2.5.1-1.e18.x8664.rpm #官网已经gg了,不更新了,请用阿里云 # wget http://rpmfind.net/linux/centos/8-stream/Base0s/x86 64/0s/Packages/libseccomp-2.5.1-1.el8.x86_64.rpm wget https://mirrors.aliyun.com/centos/8/BaseOS/x86_64/os/Packages/libseccomp-2.5.1-1.el8.x86_64.rpm cd /root/rpms sudo yum localinstall libseccomp-2.5.1-1.el8.x86_64.rpm -y #rocky 默认版本就是2.5.2 无需执行上面的命令 直接执行下面的命令查看版本 [root@k8s-01 ~]# rpm -qa | grep libseccomp libseccomp-2.5.2-2.el9.x86_64 安装方式一:(基于阿里云的源)推荐用这种方式,安装的是4sudo dnf config-manager --set-enabled powertools # Rocky Linux 8/9需启用PowerTools仓库 sudo dnf install -y yum-utils device-mapper-persistent-data lvm2 #1、卸载之前的 dnf remove docker docker-ce containerd docker-common docker-selinux docker-engine -y #2、准备repo sudo tee /etc/yum.repos.d/docker-ce.repo <<-'EOF' [docker-ce-stable] name=Docker CE Stable - AliOS baseurl=https://mirrors.aliyun.com/docker-ce/linux/centos/$releasever/$basearch/stable enabled=1 gpgcheck=1 gpgkey=https://mirrors.aliyun.com/docker-ce/linux/centos/gpg EOF # 3、安装 sudo dnf install -y containerd.io sudo dnf install containerd* -y配置# 1、配置 mkdir -pv /etc/containerd containerd config default > /etc/containerd/config.toml #为containerd生成配置文件 #2、替换默认pause镜像地址:这一步非常非常非常非常重要 grep sandbox_image /etc/containerd/config.toml sed -i 's/registry.k8s.io/registry.cn-hangzhou.aliyuncs.com\/google_containers/' /etc/containerd/config.toml grep sandbox_image /etc/containerd/config.toml #请务必确认新地址是可用的: sandbox_image="registry.cn-hangzhou.aliyuncs.com/google_containers/pause:3.6" #3、配置systemd作为容器的cgroup driver grep SystemdCgroup /etc/containerd/config.toml sed -i 's/SystemdCgroup \= false/SystemdCgroup \= true/' /etc/containerd/config.toml grep SystemdCgroup /etc/containerd/config.toml # 4、配置加速器(必须配置,否则后续安装cni网络插件时无法从docker.io里下载镜像) #参考:https://github.com/containerd/containerd/blob/main/docs/cri/config.md#registry-configuration #添加 config_path="/etc/containerd/certs.d" sed -i 's/config_path\ =.*/config_path = \"\/etc\/containerd\/certs.d\"/g' /etc/containerd/config.tomlmkdir -p /etc/containerd/certs.d/docker.io cat>/etc/containerd/certs.d/docker.io/hosts.toml << EOF server ="https://docker.io" [host."https ://dockerproxy.com"] capabilities = ["pull","resolve"] [host."https://docker.m.daocloud.io"] capabilities = ["pull","resolve"] [host."https://docker.chenby.cn"] capabilities = ["pull","resolve"] [host."https://registry.docker-cn.com"] capabilities = ["pull","resolve" ] [host."http://hub-mirror.c.163.com"] capabilities = ["pull","resolve" ] EOF#5、配置containerd开机自启动 #5.1 启动containerd服务并配置开机自启动 systemctl daemon-reload && systemctl restart containerd systemctl enable --now containerd #5.2 查看containerd状态 systemctl status containerd #5.3查看containerd的版本 ctr version五、安装k8s 5.1准备k8s源# 创建repo文件 cat <<EOF | sudo tee /etc/yum.repos.d/kubernetes.repo [kubernetes] name=Kubernetes baseurl=https://mirrors.aliyun.com/kubernetes/yum/repos/kubernetes-el7-x86_64/ enabled=1 gpgcheck=1 repo_gpgcheck=1 gpgkey=https://mirrors.aliyun.com/kubernetes/yum/doc/yum-key.gpg https://mirrors.aliyun.com/kubernetes/yum/doc/rpm-package-key.gpg EOF sudo dnf makecache #参考:https://developer.aliyun.com/mirror/kubernetes/setenforce dnf install -y kubelet-1.27* kubeadm-1.27* kubectl-1.27* systemctl enable kubelet && systemctl start kubelet && systemctl status kubelet 安装锁定版本的插件 sudo dnf install -y dnf-plugin-versionlock 锁定版本不让后续更新sudo dnf versionlock add kubelet-1.27* kubeadm-1.27* kubectl-1.27* containerd.io [root@k8s-01 ~]# sudo dnf versionlock list Last metadata expiration check: 0:35:21 ago on Fri Aug 8 10:40:25 2025. kubelet-0:1.27.6-0.* kubeadm-0:1.27.6-0.* kubectl-0:1.27.6-0.* containerd.io-0:1.7.27-3.1.el9.* #sudo dnf update就会排除锁定的应用5.2加载内核# 加载 br_netfilter 模块 sudo modprobe br_netfilter # 启用内核参数 cat <<EOF | sudo tee /etc/sysctl.d/k8s.conf net.bridge.bridge-nf-call-iptables = 1 net.bridge.bridge-nf-call-ip6tables = 1 net.ipv4.ip_forward = 1 EOF # 应用配置 sudo sysctl --system #临时关闭防火墙 sudo systemctl stop firewalld #永久关闭防火墙 sudo systemctl disable firewalld sudo modprobe br_netfilter cat <<EOF | sudo tee /etc/sysctl.d/k8s.conf net.bridge.bridge-nf-call-iptables = 1 net.bridge.bridge-nf-call-ip6tables = 1 net.ipv4.ip_forward = 1 EOF sudo sysctl --system sudo systemctl stop firewalld sudo systemctl disable firewalld 5.3主节点操作(node节点不执行)初始化master节点(仅在master节点上执行) #可以kubeadm config images list查看 [root@k8s-master-01 ~]# kubeadm config images list registry.k8s.io/kube-apiserver:v1.30.0 registry.k8s.io/kube-controller-manager:v1.30.0 registry.k8s.io/kube-scheduler:v1.30.0 registry.k8s.io/kube-proxy:v1.30.0 registry.k8s.io/coredns/coredns:v1.11.1 registry.k8s.io/pause:3.9 registry.k8s.io/etcd:3.5.12-0kubeadm config print init-defaults > kubeadm.yamlvi kubeadm.yaml apiVersion: kubeadm.k8s.io/v1beta3 bootstrapTokens: - groups: - system:bootstrappers:kubeadm:default-node-token token: abcdef.0123456789abcdef ttl: 24h0m0s apiVersion: kubeadm.k8s.io/v1beta3 bootstrapTokens: - groups: - system:bootstrappers:kubeadm:default-node-token token: abcdef.0123456789abcdef ttl: 24h0m0s usages: - signing - authentication kind: InitConfiguration localAPIEndpoint: advertiseAddress: 192.168.110.97 #这里要改为控制节点 bindPort: 6443 nodeRegistration: criSocket: unix:///var/run/containerd/containerd.sock imagePullPolicy: IfNotPresent name: k8s-master-01 #这里要修改 taints: null --- apiServer: timeoutForControlPlane: 4m0s apiVersion: kubeadm.k8s.io/v1beta3 certificatesDir: /etc/kubernetes/pki clusterName: kubernetes controllerManager: {} dns: {} etcd: local: dataDir: /var/lib/etcd imageRepository: registry.cn-hangzhou.aliyuncs.com/google_containers #要去阿里云创建仓库 kind: ClusterConfiguration kubernetesVersion: 1.30.3 networking: dnsDomain: cluster.local serviceSubnet: 10.96.0.0/12 podSubnet: 10.244.0.0/16 #添加这行 scheduler: {} #在最后插入以下内容 --- apiVersion: kubeproxy.config.k8s.io/v1alpha1 kind: KubeProxyConfiguration mode: ipvs --- apiVersion: kubelet.config.k8s.io/v1beta1 kind: KubeletConfiguration cgroupDriver: systemd部署K8Skubeadm init --config=kubeadm.yaml --ignore-preflight-errors=SystemVerification --ignore-preflight-errors=Swap部署网络插件下载网络插件wget https://github.com/flannel-io/flannel/releases/latest/download/kube-flannel.yml[root@k8s-01 ~]# cat kube-flannel.yml apiVersion: v1 kind: Namespace metadata: labels: k8s-app: flannel pod-security.kubernetes.io/enforce: privileged name: kube-flannel --- apiVersion: v1 kind: ServiceAccount metadata: labels: k8s-app: flannel name: flannel namespace: kube-flannel --- apiVersion: rbac.authorization.k8s.io/v1 kind: ClusterRole metadata: labels: k8s-app: flannel name: flannel rules: - apiGroups: - "" resources: - pods verbs: - get - apiGroups: - "" resources: - nodes verbs: - get - list - watch - apiGroups: - "" resources: - nodes/status verbs: - patch --- apiVersion: rbac.authorization.k8s.io/v1 kind: ClusterRoleBinding metadata: labels: k8s-app: flannel name: flannel roleRef: apiGroup: rbac.authorization.k8s.io kind: ClusterRole name: flannel subjects: - kind: ServiceAccount name: flannel namespace: kube-flannel --- apiVersion: v1 data: cni-conf.json: | { "name": "cbr0", "cniVersion": "0.3.1", "plugins": [ { "type": "flannel", "delegate": { "hairpinMode": true, "isDefaultGateway": true } }, { "type": "portmap", "capabilities": { "portMappings": true } } ] } net-conf.json: | { "Network": "10.244.0.0/16", "EnableNFTables": false, "Backend": { "Type": "vxlan" } } kind: ConfigMap metadata: labels: app: flannel k8s-app: flannel tier: node name: kube-flannel-cfg namespace: kube-flannel --- apiVersion: apps/v1 kind: DaemonSet metadata: labels: app: flannel k8s-app: flannel tier: node name: kube-flannel-ds namespace: kube-flannel spec: selector: matchLabels: app: flannel k8s-app: flannel template: metadata: labels: app: flannel k8s-app: flannel tier: node spec: affinity: nodeAffinity: requiredDuringSchedulingIgnoredDuringExecution: nodeSelectorTerms: - matchExpressions: - key: kubernetes.io/os operator: In values: - linux containers: - args: - --ip-masq - --kube-subnet-mgr command: - /opt/bin/flanneld env: - name: POD_NAME valueFrom: fieldRef: fieldPath: metadata.name - name: POD_NAMESPACE valueFrom: fieldRef: fieldPath: metadata.namespace - name: EVENT_QUEUE_DEPTH value: "5000" image: registry.cn-guangzhou.aliyuncs.com/xingcangku/cccc:0.25.5 name: kube-flannel resources: requests: cpu: 100m memory: 50Mi securityContext: capabilities: add: - NET_ADMIN - NET_RAW privileged: false volumeMounts: - mountPath: /run/flannel name: run - mountPath: /etc/kube-flannel/ name: flannel-cfg - mountPath: /run/xtables.lock name: xtables-lock hostNetwork: true initContainers: - args: - -f - /flannel - /opt/cni/bin/flannel command: - cp image: registry.cn-guangzhou.aliyuncs.com/xingcangku/ddd:1.5.1 name: install-cni-plugin volumeMounts: - mountPath: /opt/cni/bin name: cni-plugin - args: - -f - /etc/kube-flannel/cni-conf.json - /etc/cni/net.d/10-flannel.conflist command: - cp image: registry.cn-guangzhou.aliyuncs.com/xingcangku/cccc:0.25.5 name: install-cni volumeMounts: - mountPath: /etc/cni/net.d name: cni - mountPath: /etc/kube-flannel/ name: flannel-cfg priorityClassName: system-node-critical serviceAccountName: flannel tolerations: - effect: NoSchedule operator: Exists volumes: - hostPath: path: /run/flannel name: run - hostPath: path: /opt/cni/bin name: cni-plugin - hostPath: path: /etc/cni/net.d name: cni - configMap: name: kube-flannel-cfg name: flannel-cfg - hostPath: path: /run/xtables.lock type: FileOrCreate name: xtables-lock[root@k8s-01 ~]# grep -i image kube-flannel.yml image: registry.cn-guangzhou.aliyuncs.com/xingcangku/cccc:0.25.5 image: registry.cn-guangzhou.aliyuncs.com/xingcangku/ddd:1.5.1 image: registry.cn-guangzhou.aliyuncs.com/xingcangku/cccc:0.25.5 #在node节点执行下面命令修改ip地址 mkdir -p $HOME/.kube scp root@192.168.30.135:/etc/kubernetes/admin.conf $HOME/.kube/config chown $(id -u):$(id -g) $HOME/.kube/configdocker安装1.卸载旧版本(如有) sudo dnf remove docker \ docker-client \ docker-client-latest \ docker-common \ docker-latest \ docker-latest-logrotate \ docker-logrotate \ docker-engine 2.安装依赖包 sudo dnf install -y dnf-plugins-core 3.添加 Docker 官方仓库 sudo dnf config-manager --add-repo https://download.docker.com/linux/centos/docker-ce.repo 或者安装阿里云的 sudo dnf config-manager --add-repo https://mirrors.aliyun.com/docker-ce/linux/centos/docker-ce.repo 4.安装 Docker 引擎 sudo dnf install -y docker-ce docker-ce-cli containerd.io 5.启动并设置开机自启 sudo systemctl start docker sudo systemctl enable docker安装docker-compose1、要先给chmod +x 执行权限 2、/usr/local/bin/docker-compose 自己传docker-compose 过去 [root@k8s-03 harbor]# sudo ./install.sh [Step 0]: checking if docker is installed ... Note: docker version: 20.10.24 [Step 1]: checking docker-compose is installed ... Note: docker-compose version: 2.24.5 [Step 2]: preparing environment ... [Step 3]: preparing harbor configs ... prepare base dir is set to /root/harbor Clearing the configuration file: /config/portal/nginx.conf Clearing the configuration file: /config/log/logrotate.conf Clearing the configuration file: /config/log/rsyslog_docker.conf Clearing the configuration file: /config/nginx/nginx.conf Clearing the configuration file: /config/core/env Clearing the configuration file: /config/core/app.conf Clearing the configuration file: /config/registry/passwd Clearing the configuration file: /config/registry/config.yml Clearing the configuration file: /config/registryctl/env Clearing the configuration file: /config/registryctl/config.yml Clearing the configuration file: /config/db/env Clearing the configuration file: /config/jobservice/env Clearing the configuration file: /config/jobservice/config.yml Generated configuration file: /config/portal/nginx.conf Generated configuration file: /config/log/logrotate.conf Generated configuration file: /config/log/rsyslog_docker.conf Generated configuration file: /config/nginx/nginx.conf Generated configuration file: /config/core/env Generated configuration file: /config/core/app.conf Generated configuration file: /config/registry/config.yml Generated configuration file: /config/registryctl/env Generated configuration file: /config/registryctl/config.yml Generated configuration file: /config/db/env Generated configuration file: /config/jobservice/env Generated configuration file: /config/jobservice/config.yml loaded secret from file: /data/secret/keys/secretkey Generated configuration file: /compose_location/docker-compose.yml Clean up the input dir [Step 4]: starting Harbor ... [+] Running 9/10 ⠸ Network harbor_harbor Created 2.3s ✔ Container harbor-log Started 0.4s ✔ Container harbor-db Started 1.3s ✔ Container harbor-portal Started 1.3s ✔ Container redis Started 1.2s ✔ Container registry Started 1.2s ✔ Container registryctl Started 1.3s ✔ Container harbor-core Started 1.6s ✔ Container nginx Started 2.1s ✔ Container harbor-jobservice Started 2.2s ✔ ----Harbor has been installed and started successfully.---- [root@k8s-03 harbor]# dockeer ps -bash: dockeer: command not found [root@k8s-03 harbor]# docker p docker: 'p' is not a docker command. See 'docker --help' [root@k8s-03 harbor]# docker ps CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES 49d3c2bd157f goharbor/nginx-photon:v2.5.0 "nginx -g 'daemon of…" 11 seconds ago Up 8 seconds (health: starting) 0.0.0.0:80->8080/tcp, :::80->8080/tcp, 0.0.0.0:443->8443/tcp, :::443->8443/tcp nginx 60a868e50223 goharbor/harbor-jobservice:v2.5.0 "/harbor/entrypoint.…" 11 seconds ago Up 8 seconds (health: starting) harbor-jobservice abf5e1d382b1 goharbor/harbor-core:v2.5.0 "/harbor/entrypoint.…" 11 seconds ago Up 8 seconds (health: starting) harbor-core 9f5415aa4086 goharbor/harbor-portal:v2.5.0 "nginx -g 'daemon of…" 11 seconds ago Up 9 seconds (health: starting) harbor-portal f4c2c38abe04 goharbor/harbor-db:v2.5.0 "/docker-entrypoint.…" 11 seconds ago Up 9 seconds (health: starting) harbor-db 74b6a076b5b2 goharbor/harbor-registryctl:v2.5.0 "/home/harbor/start.…" 11 seconds ago Up 8 seconds (health: starting) registryctl 8c3bead9c56e goharbor/redis-photon:v2.5.0 "redis-server /etc/r…" 11 seconds ago Up 9 seconds (health: starting) redis d09c4161d411 goharbor/registry-photon:v2.5.0 "/home/harbor/entryp…" 11 seconds ago Up 9 seconds (health: starting) registry 90f8c13f0490 goharbor/harbor-log:v2.5.0 "/bin/sh -c /usr/loc…" 11 seconds ago Up 9 seconds (health: starting) 127.0.0.1:1514->10514/tcp harbor-log [root@k8s-03 harbor]# sudo wget "https://github.com/docker/compose/releases/download/v2.24.5/docker-compose-$(uname -s)-$(uname -m)" -O /usr/local/bin/docker-compose --2025-08-11 16:12:21-- https://github.com/docker/compose/releases/download/v2.24.5/docker-compose-Linux-x86_64 Resolving github.com (github.com)... 20.200.245.247 Connecting to github.com (github.com)|20.200.245.247|:443... connected. HTTP request sent, awaiting response... 302 Found Location: https://release-assets.githubusercontent.com/github-production-release-asset/15045751/aef9c31b-3422-45af-b239-516f7a79cca1?sp=r&sv=2018-11-09&sr=b&spr=https&se=2025-08-11T08%3A49%3A34Z&rscd=attachment%3B+filename%3Ddocker-compose-linux-x86_64&rsct=application%2Foctet-stream&skoid=96c2d410-5711-43a1-aedd-ab1947aa7ab0&sktid=398a6654-997b-47e9-b12b-9515b896b4de&skt=2025-08-11T07%3A49%3A31Z&ske=2025-08-11T08%3A49%3A34Z&sks=b&skv=2018-11-09&sig=k%2BvfmI39lbdCBNCQDwuQiB5UfH%2F8S9PNPOgAFydaPJs%3D&jwt=eyJ0eXAiOiJKV1QiLCJhbGciOiJIUzI1NiJ9.eyJpc3MiOiJnaXRodWIuY29tIiwiYXVkIjoicmVsZWFzZS1hc3NldHMuZ2l0aHVidXNlcmNvbnRlbnQuY29tIiwia2V5Ijoia2V5MSIsImV4cCI6MTc1NDkwMDI0MiwibmJmIjoxNzU0ODk5OTQyLCJwYXRoIjoicmVsZWFzZWFzc2V0cHJvZHVjdGlvbi5ibG9iLmNvcmUud2luZG93cy5uZXQifQ.x2Izppyvpu0u8fDdEvN9JVDiEOk70qV6l1OyQSg1woI&response-content-disposition=attachment%3B%20filename%3Ddocker-compose-linux-x86_64&response-content-type=application%2Foctet-stream [following] --2025-08-11 16:12:22-- https://release-assets.githubusercontent.com/github-production-release-asset/15045751/aef9c31b-3422-45af-b239-516f7a79cca1?sp=r&sv=2018-11-09&sr=b&spr=https&se=2025-08-11T08%3A49%3A34Z&rscd=attachment%3B+filename%3Ddocker-compose-linux-x86_64&rsct=application%2Foctet-stream&skoid=96c2d410-5711-43a1-aedd-ab1947aa7ab0&sktid=398a6654-997b-47e9-b12b-9515b896b4de&skt=2025-08-11T07%3A49%3A31Z&ske=2025-08-11T08%3A49%3A34Z&sks=b&skv=2018-11-09&sig=k%2BvfmI39lbdCBNCQDwuQiB5UfH%2F8S9PNPOgAFydaPJs%3D&jwt=eyJ0eXAiOiJKV1QiLCJhbGciOiJIUzI1NiJ9.eyJpc3MiOiJnaXRodWIuY29tIiwiYXVkIjoicmVsZWFzZS1hc3NldHMuZ2l0aHVidXNlcmNvbnRlbnQuY29tIiwia2V5Ijoia2V5MSIsImV4cCI6MTc1NDkwMDI0MiwibmJmIjoxNzU0ODk5OTQyLCJwYXRoIjoicmVsZWFzZWFzc2V0cHJvZHVjdGlvbi5ibG9iLmNvcmUud2luZG93cy5uZXQifQ.x2Izppyvpu0u8fDdEvN9JVDiEOk70qV6l1OyQSg1woI&response-content-disposition=attachment%3B%20filename%3Ddocker-compose-linux-x86_64&response-content-type=application%2Foctet-stream Resolving release-assets.githubusercontent.com (release-assets.githubusercontent.com)... 185.199.110.133, 185.199.111.133, 185.199.109.133, ... Connecting to release-assets.githubusercontent.com (release-assets.githubusercontent.com)|185.199.110.133|:443... connected. HTTP request sent, awaiting response... 200 OK Length: 61389086 (59M) [application/octet-stream] Saving to: ‘/usr/local/bin/docker-compose’ /usr/local/bin/docker-compose 100%[=================================================================================================================================================================>] 58.54M 164KB/s in 2m 49s 2025-08-11 16:15:11 (355 KB/s) - ‘/usr/local/bin/docker-compose’ saved [61389086/61389086] [root@k8s-03 harbor]# sudo chmod +x /usr/local/bin/docker-compose [root@k8s-03 harbor]# sudo rm -f /usr/bin/docker-compose [root@k8s-03 harbor]# sudo ln -s /usr/local/bin/docker-compose /usr/bin/docker-compose [root@k8s-03 harbor]# echo $PATH /root/.local/bin:/root/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/root/.local/bin [root@k8s-03 harbor]# docker-compose version -bash: /root/.local/bin/docker-compose: No such file or directory [root@k8s-03 harbor]# export PATH=/usr/local/bin:/usr/bin:/root/.local/bin:$PATH [root@k8s-03 harbor]# echo 'export PATH=/usr/local/bin:$PATH' | sudo tee -a /root/.bashrc export PATH=/usr/local/bin:$PATH [root@k8s-03 harbor]# source /root/.bashrc [root@k8s-03 harbor]# docker-compose version Docker Compose version v2.24.5 [root@k8s-03 harbor]# 获取证书[root@k8s-03 harbor]# sudo ./t.sh Certificate request self-signature ok subject=C=CN, ST=Beijing, L=Beijing, O=example, OU=Personal, CN=harbor.telewave.tech [root@k8s-03 harbor]# ls LICENSE common common.sh data docker-compose.yml harbor.v2.5.0.tar harbor.yml harbor.yml.bak harbor.yml.tmpl install.sh prepare t.sh [root@k8s-03 harbor]# pwd /root/harbor [root@k8s-03 harbor]# ls /work/harbor/cert/ ca.crt ca.key ca.srl harbor.telewave.tech.cert harbor.telewave.tech.crt harbor.telewave.tech.csr harbor.telewave.tech.key v3.ext
Rocky Linux 9.3 安装k8s-docker安装 一、固定IP地址#配置 sudo nmcli connection modify ens160 \ ipv4.method manual \ ipv4.addresses 192.168.30.20/24 \ ipv4.gateway 192.168.30.2 \ ipv4.dns "8.8.8.8,8.8.4.4" #更新配置 sudo nmcli connection down ens160 && sudo nmcli connection up ens160二、配置yum源 2.1备份现有仓库配置文件#sudo mkdir /etc/yum.repos.d/backup #sudo mv /etc/yum.repos.d/*.repo /etc/yum.repos.d/backup/ 直接执行下面的2.2修改仓库配置文件# 使用阿里云推荐的配置方法 sudo sed -e 's!^mirrorlist=!#mirrorlist=!g' \ -e 's!^#baseurl=http://dl.rockylinux.org/$contentdir!baseurl=https://mirrors.aliyun.com/rockylinux!g' \ -i /etc/yum.repos.d/Rocky-*.repo2.3清理并重建缓存sudo dnf clean all sudo dnf makecache2.4测试更新sudo dnf update -y三、准备工作 3.1修改主机名hostnamectl set-hostname k8s-01 hostnamectl set-hostname k8s-02 hostnamectl set-hostname k8s-033.2关闭一些服务# 1、关闭selinux sed -i 's#enforcing#disabled#g' /etc/selinux/config setenforce 0 # 2、禁用防火墙,网络管理,邮箱 systemctl disable --now firewalld NetworkManager postfix # 3、关闭swap分区 swapoff -a # 注释swap分区 cp /etc/fstab /etc/fstab_bak sed -i '/swap/d' /etc/fstab3.3sshd服务优化(可以不做)# 1、加速访问 sed -ri 's@^#UseDNS yes@UseDNS no@g' /etc/ssh/sshd_config sed -ri 's#^GSSAPIAuthentication yes#GSSAPIAuthentication no#g' /etc/ssh/sshd_config grep ^UseDNS /etc/ssh/sshd_config grep ^GSSAPIAuthentication /etc/ssh/sshd_config systemctl restart sshd # 2、密钥登录(主机点做):为了让后续一些远程拷贝操作更方便 ssh-keygen ssh-copy-id -i root@k8s-01 ssh-copy-id -i root@k8s-02 ssh-copy-id -i root@k8s-03 #连接测试 [root@m01 ~]# ssh 172.16.1.7 Last login: Tue Nov 24 09:02:26 2020 from 10.0.0.1 [root@web01 ~]#3.4增大文件标识符数量(退出当前会话立即生效)cat > /etc/security/limits.d/k8s.conf <<EOF * soft nofile 65535 * hard nofile 131070 EOF ulimit -Sn ulimit -Hn3.5所有节点配置模块自动加载,此步骤不做的话(kubeadm init时会直接失败)modprobe br_netfilter modprobe ip_conntrack cat >>/etc/rc.sysinit<<EOF #!/bin/bash for file in /etc/sysconfig/modules/*.modules ; do [ -x $file ] && $file done EOF echo "modprobe br_netfilter" >/etc/sysconfig/modules/br_netfilter.modules echo "modprobe ip_conntrack" >/etc/sysconfig/modules/ip_conntrack.modules chmod 755 /etc/sysconfig/modules/br_netfilter.modules chmod 755 /etc/sysconfig/modules/ip_conntrack.modules lsmod | grep br_netfilter3.6同步集群时间# =====================》chrony服务端:服务端我们可以自己搭建,也可以直接用公网上的时间服务器,所以是否部署服务端看你自己 # 1、安装 dnf -y install chrony # 2、修改配置文件 mv /etc/chrony.conf /etc/chrony.conf.bak cat > /etc/chrony.conf << EOF server ntp1.aliyun.com iburst minpoll 4 maxpoll 10 server ntp2.aliyun.com iburst minpoll 4 maxpoll 10 server ntp3.aliyun.com iburst minpoll 4 maxpoll 10 server ntp4.aliyun.com iburst minpoll 4 maxpoll 10 server ntp5.aliyun.com iburst minpoll 4 maxpoll 10 server ntp6.aliyun.com iburst minpoll 4 maxpoll 10 server ntp7.aliyun.com iburst minpoll 4 maxpoll 10 driftfile /var/lib/chrony/drift makestep 10 3 rtcsync allow 0.0.0.0/0 local stratum 10 keyfile /etc/chrony.keys logdir /var/log/chrony stratumweight 0.05 noclientlog logchange 0.5 EOF # 4、启动chronyd服务 systemctl restart chronyd.service # 最好重启,这样无论原来是否启动都可以重新加载配置 systemctl enable chronyd.service systemctl status chronyd.service # =====================》chrony客户端:在需要与外部同步时间的机器上安装,启动后会自动与你指定的服务端同步时间 # 下述步骤一次性粘贴到每个客户端执行即可 # 1、安装chrony dnf -y install chrony # 2、需改客户端配置文件 mv /etc/chrony.conf /etc/chrony.conf.bak cat > /etc/chrony.conf << EOF server 192.168.30.20 iburst driftfile /var/lib/chrony/drift makestep 10 3 rtcsync local stratum 10 keyfile /etc/chrony.key logdir /var/log/chrony stratumweight 0.05 noclientlog logchange 0.5 EOF # 3、启动chronyd systemctl restart chronyd.service systemctl enable chronyd.service systemctl status chronyd.service # 4、验证 chronyc sources -v3.7安装常用软件dnf -y install expect wget jq psmisc vim net-tools telnet yum-utils device-mapper-persistent-data lvm2 git ntpdate chrony bind-utils rsync unzip git3.8查看内核版本要4.4+[root@localhost ~]# grubby --default-kernel /boot/vmlinuz-5.14.0-570.30.1.el9_6.x86_643.8节点安装IPVS# 1、安装ipvsadm等相关工具 dnf -y install ipvsadm ipset sysstat conntrack libseccomp # 2、配置加载 cat > /etc/sysconfig/modules/ipvs.modules <<"EOF" #!/bin/bash ipvs_modules="ip_vs ip_vs_lc ip_vs_wlc ip_vs_rr ip_vs_wrr ip_vs_lblc ip_vs_lblcr ip_vs_dh ip_vs_sh ip_vs_fo ip_vs_nq ip_vs_sed ip_vs_ftp nf_conntrack" for kernel_module in ${ipvs_modules}; do /sbin/modinfo -F filename ${kernel_module} > /dev/null 2>&1 if [ $? -eq 0 ]; then /sbin/modprobe ${kernel_module} fi done EOF chmod 755 /etc/sysconfig/modules/ipvs.modules && bash /etc/sysconfig/modules/ipvs.modules && lsmod | grep ip_vs3.9机器修改内核参数cat > /etc/sysctl.d/k8s.conf << EOF net.ipv4.ip_forward = 1 net.bridge.bridge-nf-call-iptables = 1 net.bridge.bridge-nf-call-ip6tables = 1 fs.may_detach_mounts = 1 vm.overcommit_memory=1 vm.panic_on_oom=0 fs.inotify.max_user_watches=89100 fs.file-max=52706963 fs.nr_open=52706963 net.ipv4.tcp_keepalive_time = 600 net.ipv4.tcp.keepaliv.probes = 3 net.ipv4.tcp_keepalive_intvl = 15 net.ipv4.tcp.max_tw_buckets = 36000 net.ipv4.tcp_tw_reuse = 1 net.ipv4.tcp.max_orphans = 327680 net.ipv4.tcp_orphan_retries = 3 net.ipv4.tcp_syncookies = 1 net.ipv4.tcp_max_syn_backlog = 16384 net.ipv4.ip_conntrack_max = 65536 net.ipv4.tcp_max_syn_backlog = 16384 net.ipv4.top_timestamps = 0 net.core.somaxconn = 16384 EOF # 立即生效 sysctl --system四、安装containerd(所有k8s节点都要做) 自Kubernetes1.24以后,K8S就不再原生支持docker了我们都知道containerd来自于docker,后被docker捐献给了云原生计算基金会(我们安装docker当然会一并安装上containerd)安装方法:centos的libseccomp的版本为2.3.1,不满足containerd的需求,需要下载2.4以上的版本即可,我这里部署2.5.1版本。 rpm -e libseccomp-2.5.1-1.el8.x86_64 --nodeps rpm -ivh libseccomp-2.5.1-1.e18.x8664.rpm #官网已经gg了,不更新了,请用阿里云 # wget http://rpmfind.net/linux/centos/8-stream/Base0s/x86 64/0s/Packages/libseccomp-2.5.1-1.el8.x86_64.rpm wget https://mirrors.aliyun.com/centos/8/BaseOS/x86_64/os/Packages/libseccomp-2.5.1-1.el8.x86_64.rpm cd /root/rpms sudo yum localinstall libseccomp-2.5.1-1.el8.x86_64.rpm -y #rocky 默认版本就是2.5.2 无需执行上面的命令 直接执行下面的命令查看版本 [root@k8s-01 ~]# rpm -qa | grep libseccomp libseccomp-2.5.2-2.el9.x86_64 安装方式一:(基于阿里云的源)推荐用这种方式,安装的是4sudo dnf config-manager --set-enabled powertools # Rocky Linux 8/9需启用PowerTools仓库 sudo dnf install -y yum-utils device-mapper-persistent-data lvm2 #1、卸载之前的 dnf remove docker docker-ce containerd docker-common docker-selinux docker-engine -y #2、准备repo sudo tee /etc/yum.repos.d/docker-ce.repo <<-'EOF' [docker-ce-stable] name=Docker CE Stable - AliOS baseurl=https://mirrors.aliyun.com/docker-ce/linux/centos/$releasever/$basearch/stable enabled=1 gpgcheck=1 gpgkey=https://mirrors.aliyun.com/docker-ce/linux/centos/gpg EOF # 3、安装 sudo dnf install -y containerd.io sudo dnf install containerd* -y配置# 1、配置 mkdir -pv /etc/containerd containerd config default > /etc/containerd/config.toml #为containerd生成配置文件 #2、替换默认pause镜像地址:这一步非常非常非常非常重要 grep sandbox_image /etc/containerd/config.toml sed -i 's/registry.k8s.io/registry.cn-hangzhou.aliyuncs.com\/google_containers/' /etc/containerd/config.toml grep sandbox_image /etc/containerd/config.toml #请务必确认新地址是可用的: sandbox_image="registry.cn-hangzhou.aliyuncs.com/google_containers/pause:3.6" #3、配置systemd作为容器的cgroup driver grep SystemdCgroup /etc/containerd/config.toml sed -i 's/SystemdCgroup \= false/SystemdCgroup \= true/' /etc/containerd/config.toml grep SystemdCgroup /etc/containerd/config.toml # 4、配置加速器(必须配置,否则后续安装cni网络插件时无法从docker.io里下载镜像) #参考:https://github.com/containerd/containerd/blob/main/docs/cri/config.md#registry-configuration #添加 config_path="/etc/containerd/certs.d" sed -i 's/config_path\ =.*/config_path = \"\/etc\/containerd\/certs.d\"/g' /etc/containerd/config.tomlmkdir -p /etc/containerd/certs.d/docker.io cat>/etc/containerd/certs.d/docker.io/hosts.toml << EOF server ="https://docker.io" [host."https ://dockerproxy.com"] capabilities = ["pull","resolve"] [host."https://docker.m.daocloud.io"] capabilities = ["pull","resolve"] [host."https://docker.chenby.cn"] capabilities = ["pull","resolve"] [host."https://registry.docker-cn.com"] capabilities = ["pull","resolve" ] [host."http://hub-mirror.c.163.com"] capabilities = ["pull","resolve" ] EOF#5、配置containerd开机自启动 #5.1 启动containerd服务并配置开机自启动 systemctl daemon-reload && systemctl restart containerd systemctl enable --now containerd #5.2 查看containerd状态 systemctl status containerd #5.3查看containerd的版本 ctr version五、安装k8s 5.1准备k8s源# 创建repo文件 cat <<EOF | sudo tee /etc/yum.repos.d/kubernetes.repo [kubernetes] name=Kubernetes baseurl=https://mirrors.aliyun.com/kubernetes/yum/repos/kubernetes-el7-x86_64/ enabled=1 gpgcheck=1 repo_gpgcheck=1 gpgkey=https://mirrors.aliyun.com/kubernetes/yum/doc/yum-key.gpg https://mirrors.aliyun.com/kubernetes/yum/doc/rpm-package-key.gpg EOF sudo dnf makecache #参考:https://developer.aliyun.com/mirror/kubernetes/setenforce dnf install -y kubelet-1.27* kubeadm-1.27* kubectl-1.27* systemctl enable kubelet && systemctl start kubelet && systemctl status kubelet 安装锁定版本的插件 sudo dnf install -y dnf-plugin-versionlock 锁定版本不让后续更新sudo dnf versionlock add kubelet-1.27* kubeadm-1.27* kubectl-1.27* containerd.io [root@k8s-01 ~]# sudo dnf versionlock list Last metadata expiration check: 0:35:21 ago on Fri Aug 8 10:40:25 2025. kubelet-0:1.27.6-0.* kubeadm-0:1.27.6-0.* kubectl-0:1.27.6-0.* containerd.io-0:1.7.27-3.1.el9.* #sudo dnf update就会排除锁定的应用5.2加载内核# 加载 br_netfilter 模块 sudo modprobe br_netfilter # 启用内核参数 cat <<EOF | sudo tee /etc/sysctl.d/k8s.conf net.bridge.bridge-nf-call-iptables = 1 net.bridge.bridge-nf-call-ip6tables = 1 net.ipv4.ip_forward = 1 EOF # 应用配置 sudo sysctl --system #临时关闭防火墙 sudo systemctl stop firewalld #永久关闭防火墙 sudo systemctl disable firewalld sudo modprobe br_netfilter cat <<EOF | sudo tee /etc/sysctl.d/k8s.conf net.bridge.bridge-nf-call-iptables = 1 net.bridge.bridge-nf-call-ip6tables = 1 net.ipv4.ip_forward = 1 EOF sudo sysctl --system sudo systemctl stop firewalld sudo systemctl disable firewalld 5.3主节点操作(node节点不执行)初始化master节点(仅在master节点上执行) #可以kubeadm config images list查看 [root@k8s-master-01 ~]# kubeadm config images list registry.k8s.io/kube-apiserver:v1.30.0 registry.k8s.io/kube-controller-manager:v1.30.0 registry.k8s.io/kube-scheduler:v1.30.0 registry.k8s.io/kube-proxy:v1.30.0 registry.k8s.io/coredns/coredns:v1.11.1 registry.k8s.io/pause:3.9 registry.k8s.io/etcd:3.5.12-0kubeadm config print init-defaults > kubeadm.yamlvi kubeadm.yaml apiVersion: kubeadm.k8s.io/v1beta3 bootstrapTokens: - groups: - system:bootstrappers:kubeadm:default-node-token token: abcdef.0123456789abcdef ttl: 24h0m0s apiVersion: kubeadm.k8s.io/v1beta3 bootstrapTokens: - groups: - system:bootstrappers:kubeadm:default-node-token token: abcdef.0123456789abcdef ttl: 24h0m0s usages: - signing - authentication kind: InitConfiguration localAPIEndpoint: advertiseAddress: 192.168.110.97 #这里要改为控制节点 bindPort: 6443 nodeRegistration: criSocket: unix:///var/run/containerd/containerd.sock imagePullPolicy: IfNotPresent name: k8s-master-01 #这里要修改 taints: null --- apiServer: timeoutForControlPlane: 4m0s apiVersion: kubeadm.k8s.io/v1beta3 certificatesDir: /etc/kubernetes/pki clusterName: kubernetes controllerManager: {} dns: {} etcd: local: dataDir: /var/lib/etcd imageRepository: registry.cn-hangzhou.aliyuncs.com/google_containers #要去阿里云创建仓库 kind: ClusterConfiguration kubernetesVersion: 1.30.3 networking: dnsDomain: cluster.local serviceSubnet: 10.96.0.0/12 podSubnet: 10.244.0.0/16 #添加这行 scheduler: {} #在最后插入以下内容 --- apiVersion: kubeproxy.config.k8s.io/v1alpha1 kind: KubeProxyConfiguration mode: ipvs --- apiVersion: kubelet.config.k8s.io/v1beta1 kind: KubeletConfiguration cgroupDriver: systemd部署K8Skubeadm init --config=kubeadm.yaml --ignore-preflight-errors=SystemVerification --ignore-preflight-errors=Swap部署网络插件下载网络插件wget https://github.com/flannel-io/flannel/releases/latest/download/kube-flannel.yml[root@k8s-01 ~]# cat kube-flannel.yml apiVersion: v1 kind: Namespace metadata: labels: k8s-app: flannel pod-security.kubernetes.io/enforce: privileged name: kube-flannel --- apiVersion: v1 kind: ServiceAccount metadata: labels: k8s-app: flannel name: flannel namespace: kube-flannel --- apiVersion: rbac.authorization.k8s.io/v1 kind: ClusterRole metadata: labels: k8s-app: flannel name: flannel rules: - apiGroups: - "" resources: - pods verbs: - get - apiGroups: - "" resources: - nodes verbs: - get - list - watch - apiGroups: - "" resources: - nodes/status verbs: - patch --- apiVersion: rbac.authorization.k8s.io/v1 kind: ClusterRoleBinding metadata: labels: k8s-app: flannel name: flannel roleRef: apiGroup: rbac.authorization.k8s.io kind: ClusterRole name: flannel subjects: - kind: ServiceAccount name: flannel namespace: kube-flannel --- apiVersion: v1 data: cni-conf.json: | { "name": "cbr0", "cniVersion": "0.3.1", "plugins": [ { "type": "flannel", "delegate": { "hairpinMode": true, "isDefaultGateway": true } }, { "type": "portmap", "capabilities": { "portMappings": true } } ] } net-conf.json: | { "Network": "10.244.0.0/16", "EnableNFTables": false, "Backend": { "Type": "vxlan" } } kind: ConfigMap metadata: labels: app: flannel k8s-app: flannel tier: node name: kube-flannel-cfg namespace: kube-flannel --- apiVersion: apps/v1 kind: DaemonSet metadata: labels: app: flannel k8s-app: flannel tier: node name: kube-flannel-ds namespace: kube-flannel spec: selector: matchLabels: app: flannel k8s-app: flannel template: metadata: labels: app: flannel k8s-app: flannel tier: node spec: affinity: nodeAffinity: requiredDuringSchedulingIgnoredDuringExecution: nodeSelectorTerms: - matchExpressions: - key: kubernetes.io/os operator: In values: - linux containers: - args: - --ip-masq - --kube-subnet-mgr command: - /opt/bin/flanneld env: - name: POD_NAME valueFrom: fieldRef: fieldPath: metadata.name - name: POD_NAMESPACE valueFrom: fieldRef: fieldPath: metadata.namespace - name: EVENT_QUEUE_DEPTH value: "5000" image: registry.cn-guangzhou.aliyuncs.com/xingcangku/cccc:0.25.5 name: kube-flannel resources: requests: cpu: 100m memory: 50Mi securityContext: capabilities: add: - NET_ADMIN - NET_RAW privileged: false volumeMounts: - mountPath: /run/flannel name: run - mountPath: /etc/kube-flannel/ name: flannel-cfg - mountPath: /run/xtables.lock name: xtables-lock hostNetwork: true initContainers: - args: - -f - /flannel - /opt/cni/bin/flannel command: - cp image: registry.cn-guangzhou.aliyuncs.com/xingcangku/ddd:1.5.1 name: install-cni-plugin volumeMounts: - mountPath: /opt/cni/bin name: cni-plugin - args: - -f - /etc/kube-flannel/cni-conf.json - /etc/cni/net.d/10-flannel.conflist command: - cp image: registry.cn-guangzhou.aliyuncs.com/xingcangku/cccc:0.25.5 name: install-cni volumeMounts: - mountPath: /etc/cni/net.d name: cni - mountPath: /etc/kube-flannel/ name: flannel-cfg priorityClassName: system-node-critical serviceAccountName: flannel tolerations: - effect: NoSchedule operator: Exists volumes: - hostPath: path: /run/flannel name: run - hostPath: path: /opt/cni/bin name: cni-plugin - hostPath: path: /etc/cni/net.d name: cni - configMap: name: kube-flannel-cfg name: flannel-cfg - hostPath: path: /run/xtables.lock type: FileOrCreate name: xtables-lock[root@k8s-01 ~]# grep -i image kube-flannel.yml image: registry.cn-guangzhou.aliyuncs.com/xingcangku/cccc:0.25.5 image: registry.cn-guangzhou.aliyuncs.com/xingcangku/ddd:1.5.1 image: registry.cn-guangzhou.aliyuncs.com/xingcangku/cccc:0.25.5 #在node节点执行下面命令修改ip地址 mkdir -p $HOME/.kube scp root@192.168.30.135:/etc/kubernetes/admin.conf $HOME/.kube/config chown $(id -u):$(id -g) $HOME/.kube/configdocker安装1.卸载旧版本(如有) sudo dnf remove docker \ docker-client \ docker-client-latest \ docker-common \ docker-latest \ docker-latest-logrotate \ docker-logrotate \ docker-engine 2.安装依赖包 sudo dnf install -y dnf-plugins-core 3.添加 Docker 官方仓库 sudo dnf config-manager --add-repo https://download.docker.com/linux/centos/docker-ce.repo 或者安装阿里云的 sudo dnf config-manager --add-repo https://mirrors.aliyun.com/docker-ce/linux/centos/docker-ce.repo 4.安装 Docker 引擎 sudo dnf install -y docker-ce docker-ce-cli containerd.io 5.启动并设置开机自启 sudo systemctl start docker sudo systemctl enable docker安装docker-compose1、要先给chmod +x 执行权限 2、/usr/local/bin/docker-compose 自己传docker-compose 过去 [root@k8s-03 harbor]# sudo ./install.sh [Step 0]: checking if docker is installed ... Note: docker version: 20.10.24 [Step 1]: checking docker-compose is installed ... Note: docker-compose version: 2.24.5 [Step 2]: preparing environment ... [Step 3]: preparing harbor configs ... prepare base dir is set to /root/harbor Clearing the configuration file: /config/portal/nginx.conf Clearing the configuration file: /config/log/logrotate.conf Clearing the configuration file: /config/log/rsyslog_docker.conf Clearing the configuration file: /config/nginx/nginx.conf Clearing the configuration file: /config/core/env Clearing the configuration file: /config/core/app.conf Clearing the configuration file: /config/registry/passwd Clearing the configuration file: /config/registry/config.yml Clearing the configuration file: /config/registryctl/env Clearing the configuration file: /config/registryctl/config.yml Clearing the configuration file: /config/db/env Clearing the configuration file: /config/jobservice/env Clearing the configuration file: /config/jobservice/config.yml Generated configuration file: /config/portal/nginx.conf Generated configuration file: /config/log/logrotate.conf Generated configuration file: /config/log/rsyslog_docker.conf Generated configuration file: /config/nginx/nginx.conf Generated configuration file: /config/core/env Generated configuration file: /config/core/app.conf Generated configuration file: /config/registry/config.yml Generated configuration file: /config/registryctl/env Generated configuration file: /config/registryctl/config.yml Generated configuration file: /config/db/env Generated configuration file: /config/jobservice/env Generated configuration file: /config/jobservice/config.yml loaded secret from file: /data/secret/keys/secretkey Generated configuration file: /compose_location/docker-compose.yml Clean up the input dir [Step 4]: starting Harbor ... [+] Running 9/10 ⠸ Network harbor_harbor Created 2.3s ✔ Container harbor-log Started 0.4s ✔ Container harbor-db Started 1.3s ✔ Container harbor-portal Started 1.3s ✔ Container redis Started 1.2s ✔ Container registry Started 1.2s ✔ Container registryctl Started 1.3s ✔ Container harbor-core Started 1.6s ✔ Container nginx Started 2.1s ✔ Container harbor-jobservice Started 2.2s ✔ ----Harbor has been installed and started successfully.---- [root@k8s-03 harbor]# dockeer ps -bash: dockeer: command not found [root@k8s-03 harbor]# docker p docker: 'p' is not a docker command. See 'docker --help' [root@k8s-03 harbor]# docker ps CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES 49d3c2bd157f goharbor/nginx-photon:v2.5.0 "nginx -g 'daemon of…" 11 seconds ago Up 8 seconds (health: starting) 0.0.0.0:80->8080/tcp, :::80->8080/tcp, 0.0.0.0:443->8443/tcp, :::443->8443/tcp nginx 60a868e50223 goharbor/harbor-jobservice:v2.5.0 "/harbor/entrypoint.…" 11 seconds ago Up 8 seconds (health: starting) harbor-jobservice abf5e1d382b1 goharbor/harbor-core:v2.5.0 "/harbor/entrypoint.…" 11 seconds ago Up 8 seconds (health: starting) harbor-core 9f5415aa4086 goharbor/harbor-portal:v2.5.0 "nginx -g 'daemon of…" 11 seconds ago Up 9 seconds (health: starting) harbor-portal f4c2c38abe04 goharbor/harbor-db:v2.5.0 "/docker-entrypoint.…" 11 seconds ago Up 9 seconds (health: starting) harbor-db 74b6a076b5b2 goharbor/harbor-registryctl:v2.5.0 "/home/harbor/start.…" 11 seconds ago Up 8 seconds (health: starting) registryctl 8c3bead9c56e goharbor/redis-photon:v2.5.0 "redis-server /etc/r…" 11 seconds ago Up 9 seconds (health: starting) redis d09c4161d411 goharbor/registry-photon:v2.5.0 "/home/harbor/entryp…" 11 seconds ago Up 9 seconds (health: starting) registry 90f8c13f0490 goharbor/harbor-log:v2.5.0 "/bin/sh -c /usr/loc…" 11 seconds ago Up 9 seconds (health: starting) 127.0.0.1:1514->10514/tcp harbor-log [root@k8s-03 harbor]# sudo wget "https://github.com/docker/compose/releases/download/v2.24.5/docker-compose-$(uname -s)-$(uname -m)" -O /usr/local/bin/docker-compose --2025-08-11 16:12:21-- https://github.com/docker/compose/releases/download/v2.24.5/docker-compose-Linux-x86_64 Resolving github.com (github.com)... 20.200.245.247 Connecting to github.com (github.com)|20.200.245.247|:443... connected. HTTP request sent, awaiting response... 302 Found Location: https://release-assets.githubusercontent.com/github-production-release-asset/15045751/aef9c31b-3422-45af-b239-516f7a79cca1?sp=r&sv=2018-11-09&sr=b&spr=https&se=2025-08-11T08%3A49%3A34Z&rscd=attachment%3B+filename%3Ddocker-compose-linux-x86_64&rsct=application%2Foctet-stream&skoid=96c2d410-5711-43a1-aedd-ab1947aa7ab0&sktid=398a6654-997b-47e9-b12b-9515b896b4de&skt=2025-08-11T07%3A49%3A31Z&ske=2025-08-11T08%3A49%3A34Z&sks=b&skv=2018-11-09&sig=k%2BvfmI39lbdCBNCQDwuQiB5UfH%2F8S9PNPOgAFydaPJs%3D&jwt=eyJ0eXAiOiJKV1QiLCJhbGciOiJIUzI1NiJ9.eyJpc3MiOiJnaXRodWIuY29tIiwiYXVkIjoicmVsZWFzZS1hc3NldHMuZ2l0aHVidXNlcmNvbnRlbnQuY29tIiwia2V5Ijoia2V5MSIsImV4cCI6MTc1NDkwMDI0MiwibmJmIjoxNzU0ODk5OTQyLCJwYXRoIjoicmVsZWFzZWFzc2V0cHJvZHVjdGlvbi5ibG9iLmNvcmUud2luZG93cy5uZXQifQ.x2Izppyvpu0u8fDdEvN9JVDiEOk70qV6l1OyQSg1woI&response-content-disposition=attachment%3B%20filename%3Ddocker-compose-linux-x86_64&response-content-type=application%2Foctet-stream [following] --2025-08-11 16:12:22-- https://release-assets.githubusercontent.com/github-production-release-asset/15045751/aef9c31b-3422-45af-b239-516f7a79cca1?sp=r&sv=2018-11-09&sr=b&spr=https&se=2025-08-11T08%3A49%3A34Z&rscd=attachment%3B+filename%3Ddocker-compose-linux-x86_64&rsct=application%2Foctet-stream&skoid=96c2d410-5711-43a1-aedd-ab1947aa7ab0&sktid=398a6654-997b-47e9-b12b-9515b896b4de&skt=2025-08-11T07%3A49%3A31Z&ske=2025-08-11T08%3A49%3A34Z&sks=b&skv=2018-11-09&sig=k%2BvfmI39lbdCBNCQDwuQiB5UfH%2F8S9PNPOgAFydaPJs%3D&jwt=eyJ0eXAiOiJKV1QiLCJhbGciOiJIUzI1NiJ9.eyJpc3MiOiJnaXRodWIuY29tIiwiYXVkIjoicmVsZWFzZS1hc3NldHMuZ2l0aHVidXNlcmNvbnRlbnQuY29tIiwia2V5Ijoia2V5MSIsImV4cCI6MTc1NDkwMDI0MiwibmJmIjoxNzU0ODk5OTQyLCJwYXRoIjoicmVsZWFzZWFzc2V0cHJvZHVjdGlvbi5ibG9iLmNvcmUud2luZG93cy5uZXQifQ.x2Izppyvpu0u8fDdEvN9JVDiEOk70qV6l1OyQSg1woI&response-content-disposition=attachment%3B%20filename%3Ddocker-compose-linux-x86_64&response-content-type=application%2Foctet-stream Resolving release-assets.githubusercontent.com (release-assets.githubusercontent.com)... 185.199.110.133, 185.199.111.133, 185.199.109.133, ... Connecting to release-assets.githubusercontent.com (release-assets.githubusercontent.com)|185.199.110.133|:443... connected. HTTP request sent, awaiting response... 200 OK Length: 61389086 (59M) [application/octet-stream] Saving to: ‘/usr/local/bin/docker-compose’ /usr/local/bin/docker-compose 100%[=================================================================================================================================================================>] 58.54M 164KB/s in 2m 49s 2025-08-11 16:15:11 (355 KB/s) - ‘/usr/local/bin/docker-compose’ saved [61389086/61389086] [root@k8s-03 harbor]# sudo chmod +x /usr/local/bin/docker-compose [root@k8s-03 harbor]# sudo rm -f /usr/bin/docker-compose [root@k8s-03 harbor]# sudo ln -s /usr/local/bin/docker-compose /usr/bin/docker-compose [root@k8s-03 harbor]# echo $PATH /root/.local/bin:/root/bin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/root/.local/bin [root@k8s-03 harbor]# docker-compose version -bash: /root/.local/bin/docker-compose: No such file or directory [root@k8s-03 harbor]# export PATH=/usr/local/bin:/usr/bin:/root/.local/bin:$PATH [root@k8s-03 harbor]# echo 'export PATH=/usr/local/bin:$PATH' | sudo tee -a /root/.bashrc export PATH=/usr/local/bin:$PATH [root@k8s-03 harbor]# source /root/.bashrc [root@k8s-03 harbor]# docker-compose version Docker Compose version v2.24.5 [root@k8s-03 harbor]# 获取证书[root@k8s-03 harbor]# sudo ./t.sh Certificate request self-signature ok subject=C=CN, ST=Beijing, L=Beijing, O=example, OU=Personal, CN=harbor.telewave.tech [root@k8s-03 harbor]# ls LICENSE common common.sh data docker-compose.yml harbor.v2.5.0.tar harbor.yml harbor.yml.bak harbor.yml.tmpl install.sh prepare t.sh [root@k8s-03 harbor]# pwd /root/harbor [root@k8s-03 harbor]# ls /work/harbor/cert/ ca.crt ca.key ca.srl harbor.telewave.tech.cert harbor.telewave.tech.crt harbor.telewave.tech.csr harbor.telewave.tech.key v3.ext -
 gitlab runner安装 安装的gitlab runner版本与gitlab版本保持一致。一、参考文档https://docs.gitlab.com/runner/install/index.html二、查看gitlab版本root@k8s-02:~# gitlab-rake gitlab:env:info System information System: Ubuntu 22.04 Current User: git Using RVM: no Ruby Version: 3.2.5 Gem Version: 3.6.9 Bundler Version:2.6.5 Rake Version: 13.0.6 Redis Version: 7.2.9 Sidekiq Version:7.3.9 Go Version: unknown GitLab information Version: 18.2.1 Revision: baccadafcda Directory: /opt/gitlab/embedded/service/gitlab-rails DB Adapter: PostgreSQL DB Version: 16.8 URL: http://192.168.30.181 HTTP Clone URL: http://192.168.30.181/some-group/some-project.git SSH Clone URL: git@192.168.30.181:some-group/some-project.git Using LDAP: no Using Omniauth: yes Omniauth Providers: GitLab Shell Version: 14.43.0 Repository storages: - default: unix:/var/opt/gitlab/gitaly/gitaly.socket GitLab Shell path: /opt/gitlab/embedded/service/gitlab-shell Gitaly - default Address: unix:/var/opt/gitlab/gitaly/gitaly.socket - default Version: 18.2.1 - default Git Version: 2.50.1.gl1 三、yum安装https://docs.gitlab.com/runner/install/linux-repository.html #centos curl -L "https://packages.gitlab.com/install/repositories/runner/gitlab-runner/script.rpm.sh" | sudo bash #ubuntu curl -L "https://packages.gitlab.com/install/repositories/runner/gitlab-runner/script.deb.sh" | sudo bash #要安装特定版本的 GitLab Runner: #centos yum list gitlab-runner --showduplicates | sort -r sudo yum install gitlab-runner-17.2.0-1 #ubuntu apt-cache madison gitlab-runner sudo apt install gitlab-runner=17.7.1-1 gitlab-runner-helper-images=17.7.1-1 root@k8s-02:~# gitlab-rake gitlab:env:info System information System: Ubuntu 22.04 Current User: git Using RVM: no Ruby Version: 3.2.5 Gem Version: 3.6.9 Bundler Version:2.6.5 Rake Version: 13.0.6 Redis Version: 7.2.9 Sidekiq Version:7.3.9 Go Version: unknown GitLab information Version: 18.2.1 Revision: baccadafcda Directory: /opt/gitlab/embedded/service/gitlab-rails DB Adapter: PostgreSQL DB Version: 16.8 URL: http://192.168.30.181 HTTP Clone URL: http://192.168.30.181/some-group/some-project.git SSH Clone URL: git@192.168.30.181:some-group/some-project.git Using LDAP: no Using Omniauth: yes Omniauth Providers: GitLab Shell Version: 14.43.0 Repository storages: - default: unix:/var/opt/gitlab/gitaly/gitaly.socket GitLab Shell path: /opt/gitlab/embedded/service/gitlab-shell Gitaly - default Address: unix:/var/opt/gitlab/gitaly/gitaly.socket - default Version: 18.2.1 - default Git Version: 2.50.1.gl1 root@k8s-02:~# systemctl status gitlab gitlab-runner.service gitlab-runsvdir.service gitlab.slice root@k8s-02:~# systemctl status gitlab gitlab-runner.service gitlab-runsvdir.service gitlab.slice root@k8s-02:~# systemctl status gitlab-runner.service ● gitlab-runner.service - GitLab Runner Loaded: loaded (/etc/systemd/system/gitlab-runner.service; enabled; vendor preset: enabled) Active: active (running) since Mon 2025-08-11 12:31:20 UTC; 32min ago Main PID: 1044 (gitlab-runner) Tasks: 10 (limit: 23452) Memory: 82.6M CPU: 3.032s CGroup: /system.slice/gitlab-runner.service └─1044 /usr/bin/gitlab-runner run --config /etc/gitlab-runner/config.toml --working-directory /home/gitlab-runner --ser> Aug 11 12:31:20 k8s-02 systemd[1]: Started GitLab Runner. Aug 11 12:31:24 k8s-02 gitlab-runner[1044]: Runtime platform arch=amd64 os=linux pid=1044 revisio> Aug 11 12:31:24 k8s-02 gitlab-runner[1044]: Starting multi-runner from /etc/gitlab-runner/config.toml... builds=0 max_builds=0 Aug 11 12:31:24 k8s-02 gitlab-runner[1044]: Running in system-mode. Aug 11 12:31:24 k8s-02 gitlab-runner[1044]: Aug 11 12:31:24 k8s-02 gitlab-runner[1044]: Usage logger disabled builds=0 max_builds=1 Aug 11 12:31:24 k8s-02 gitlab-runner[1044]: Configuration loaded builds=0 max_builds=1 Aug 11 12:31:24 k8s-02 gitlab-runner[1044]: listen_address not defined, metrics & debug endpoints disabled builds=0 max_builds=1 Aug 11 12:31:24 k8s-02 gitlab-runner[1044]: [session_server].listen_address not defined, session endpoints disabled builds=0 max_bu> Aug 11 12:31:24 k8s-02 gitlab-runner[1044]: Initializing executor providers builds=0 max_builds=1 root@k8s-02:~# ^C root@k8s-02:~# gitlab-runner -v Version: 18.2.1 Git revision: cc489270 Git branch: 18-2-stable GO version: go1.24.4 X:cacheprog Built: 2025-07-28T12:43:39Z OS/Arch: linux/amd64 如果您尝试安装的特定版本gitlab-runner而不安装相同版本的 gitlab-runner-helper-images,则可能会遇到以下错误: sudo apt install gitlab-runner=17.7.1-1 ... The following packages have unmet dependencies: gitlab-runner : Depends: gitlab-runner-helper-images (= 17.7.1-1) but 17.8.3-1 is to be installed E: Unable to correct problems, you have held broken packages.四、rpm包安装查找合适版本的软件包并下载 https://mirrors.tuna.tsinghua.edu.cn/gitlab-runner/yum/el7-x86_64/ [root@tiaoban gitlab-runner]# wget https://mirrors.tuna.tsinghua.edu.cn/gitlab-runner/yum/el7-x86_64/gitlab-runner-16.10.0-1.x86_64.rpm [root@tiaoban gitlab-runner]# rpm -ivh gitlab-runner-16.10.0-1.x86_64.rpm五、docker安装[root@client2 docker]# mkdir gitlab-runner [root@client2 docker]# ls gitlab-runner [root@client2 docker]# docker run --name gitlab-runner -itd -v /opt/docker/gitlab-runner:/etc/gitlab-runner --restart always gitlab/gitlab-runner:v16.10.0
gitlab runner安装 安装的gitlab runner版本与gitlab版本保持一致。一、参考文档https://docs.gitlab.com/runner/install/index.html二、查看gitlab版本root@k8s-02:~# gitlab-rake gitlab:env:info System information System: Ubuntu 22.04 Current User: git Using RVM: no Ruby Version: 3.2.5 Gem Version: 3.6.9 Bundler Version:2.6.5 Rake Version: 13.0.6 Redis Version: 7.2.9 Sidekiq Version:7.3.9 Go Version: unknown GitLab information Version: 18.2.1 Revision: baccadafcda Directory: /opt/gitlab/embedded/service/gitlab-rails DB Adapter: PostgreSQL DB Version: 16.8 URL: http://192.168.30.181 HTTP Clone URL: http://192.168.30.181/some-group/some-project.git SSH Clone URL: git@192.168.30.181:some-group/some-project.git Using LDAP: no Using Omniauth: yes Omniauth Providers: GitLab Shell Version: 14.43.0 Repository storages: - default: unix:/var/opt/gitlab/gitaly/gitaly.socket GitLab Shell path: /opt/gitlab/embedded/service/gitlab-shell Gitaly - default Address: unix:/var/opt/gitlab/gitaly/gitaly.socket - default Version: 18.2.1 - default Git Version: 2.50.1.gl1 三、yum安装https://docs.gitlab.com/runner/install/linux-repository.html #centos curl -L "https://packages.gitlab.com/install/repositories/runner/gitlab-runner/script.rpm.sh" | sudo bash #ubuntu curl -L "https://packages.gitlab.com/install/repositories/runner/gitlab-runner/script.deb.sh" | sudo bash #要安装特定版本的 GitLab Runner: #centos yum list gitlab-runner --showduplicates | sort -r sudo yum install gitlab-runner-17.2.0-1 #ubuntu apt-cache madison gitlab-runner sudo apt install gitlab-runner=17.7.1-1 gitlab-runner-helper-images=17.7.1-1 root@k8s-02:~# gitlab-rake gitlab:env:info System information System: Ubuntu 22.04 Current User: git Using RVM: no Ruby Version: 3.2.5 Gem Version: 3.6.9 Bundler Version:2.6.5 Rake Version: 13.0.6 Redis Version: 7.2.9 Sidekiq Version:7.3.9 Go Version: unknown GitLab information Version: 18.2.1 Revision: baccadafcda Directory: /opt/gitlab/embedded/service/gitlab-rails DB Adapter: PostgreSQL DB Version: 16.8 URL: http://192.168.30.181 HTTP Clone URL: http://192.168.30.181/some-group/some-project.git SSH Clone URL: git@192.168.30.181:some-group/some-project.git Using LDAP: no Using Omniauth: yes Omniauth Providers: GitLab Shell Version: 14.43.0 Repository storages: - default: unix:/var/opt/gitlab/gitaly/gitaly.socket GitLab Shell path: /opt/gitlab/embedded/service/gitlab-shell Gitaly - default Address: unix:/var/opt/gitlab/gitaly/gitaly.socket - default Version: 18.2.1 - default Git Version: 2.50.1.gl1 root@k8s-02:~# systemctl status gitlab gitlab-runner.service gitlab-runsvdir.service gitlab.slice root@k8s-02:~# systemctl status gitlab gitlab-runner.service gitlab-runsvdir.service gitlab.slice root@k8s-02:~# systemctl status gitlab-runner.service ● gitlab-runner.service - GitLab Runner Loaded: loaded (/etc/systemd/system/gitlab-runner.service; enabled; vendor preset: enabled) Active: active (running) since Mon 2025-08-11 12:31:20 UTC; 32min ago Main PID: 1044 (gitlab-runner) Tasks: 10 (limit: 23452) Memory: 82.6M CPU: 3.032s CGroup: /system.slice/gitlab-runner.service └─1044 /usr/bin/gitlab-runner run --config /etc/gitlab-runner/config.toml --working-directory /home/gitlab-runner --ser> Aug 11 12:31:20 k8s-02 systemd[1]: Started GitLab Runner. Aug 11 12:31:24 k8s-02 gitlab-runner[1044]: Runtime platform arch=amd64 os=linux pid=1044 revisio> Aug 11 12:31:24 k8s-02 gitlab-runner[1044]: Starting multi-runner from /etc/gitlab-runner/config.toml... builds=0 max_builds=0 Aug 11 12:31:24 k8s-02 gitlab-runner[1044]: Running in system-mode. Aug 11 12:31:24 k8s-02 gitlab-runner[1044]: Aug 11 12:31:24 k8s-02 gitlab-runner[1044]: Usage logger disabled builds=0 max_builds=1 Aug 11 12:31:24 k8s-02 gitlab-runner[1044]: Configuration loaded builds=0 max_builds=1 Aug 11 12:31:24 k8s-02 gitlab-runner[1044]: listen_address not defined, metrics & debug endpoints disabled builds=0 max_builds=1 Aug 11 12:31:24 k8s-02 gitlab-runner[1044]: [session_server].listen_address not defined, session endpoints disabled builds=0 max_bu> Aug 11 12:31:24 k8s-02 gitlab-runner[1044]: Initializing executor providers builds=0 max_builds=1 root@k8s-02:~# ^C root@k8s-02:~# gitlab-runner -v Version: 18.2.1 Git revision: cc489270 Git branch: 18-2-stable GO version: go1.24.4 X:cacheprog Built: 2025-07-28T12:43:39Z OS/Arch: linux/amd64 如果您尝试安装的特定版本gitlab-runner而不安装相同版本的 gitlab-runner-helper-images,则可能会遇到以下错误: sudo apt install gitlab-runner=17.7.1-1 ... The following packages have unmet dependencies: gitlab-runner : Depends: gitlab-runner-helper-images (= 17.7.1-1) but 17.8.3-1 is to be installed E: Unable to correct problems, you have held broken packages.四、rpm包安装查找合适版本的软件包并下载 https://mirrors.tuna.tsinghua.edu.cn/gitlab-runner/yum/el7-x86_64/ [root@tiaoban gitlab-runner]# wget https://mirrors.tuna.tsinghua.edu.cn/gitlab-runner/yum/el7-x86_64/gitlab-runner-16.10.0-1.x86_64.rpm [root@tiaoban gitlab-runner]# rpm -ivh gitlab-runner-16.10.0-1.x86_64.rpm五、docker安装[root@client2 docker]# mkdir gitlab-runner [root@client2 docker]# ls gitlab-runner [root@client2 docker]# docker run --name gitlab-runner -itd -v /opt/docker/gitlab-runner:/etc/gitlab-runner --restart always gitlab/gitlab-runner:v16.10.0 -
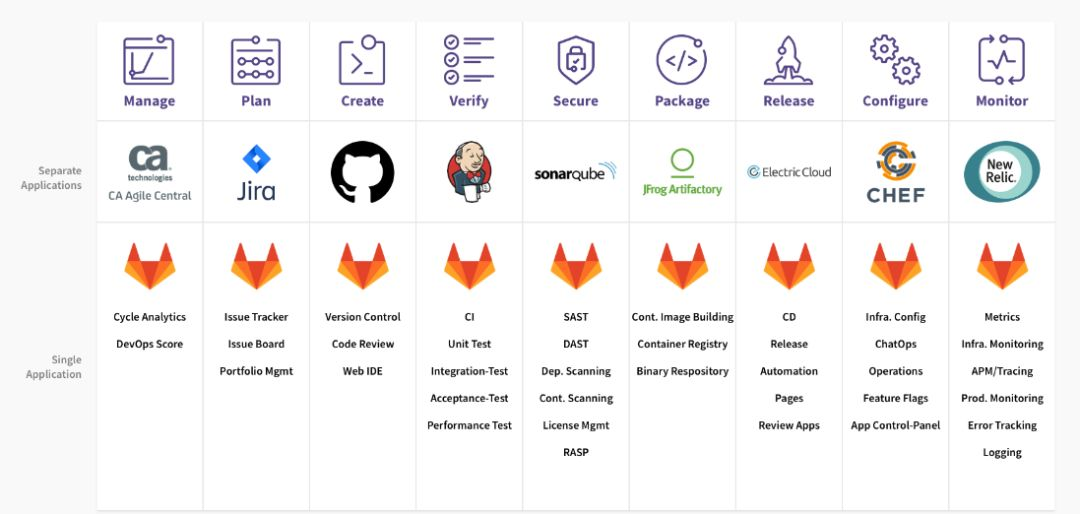
 Gitlab CI/CD简介和jenkins对比 一、Gitlab CI/CD优势- 开源: CI/CD是开源GitLab社区版和专有GitLab企业版的一部分。 - 易于学习: 具有详细的入门文档。 - 无缝集成: GitLab CI / CD是GitLab的一部分,支持从计划到部署,具有出色的用户体验。 - 可扩展: 测试可以在单独的计算机上分布式运行,可以根据需要添加任意数量的计算机。 - 更快的结果: 每个构建可以拆分为多个作业,这些作业可以在多台计算机上并行运行。 - 针对交付进行了优化: 多个阶段,手动部署, 环境 和 变量。二、Gitlab CI/CD特点- 多平台: Unix,Windows,macOS和任何其他支持Go的平台上执行构建。 - 多语言: 构建脚本是命令行驱动的,并且可以与Java,PHP,Ruby,C和任何其他语言一起使用。 - 稳定构建: 构建在与GitLab不同的机器上运行。 - 并行构建: GitLab CI / CD在多台机器上拆分构建,以实现快速执行。 - 实时日志记录: 合并请求中的链接将您带到动态更新的当前构建日志。 - 灵活的管道: 您可以在每个阶段定义多个并行作业,并且可以 触发其他构建。 - 版本管道: 一个 .gitlab-ci.yml文件 包含您的测试,整个过程的步骤,使每个人都能贡献更改,并确保每个分支获得所需的管道。 - 自动缩放: 您可以 自动缩放构建机器,以确保立即处理您的构建并将成本降至最低。 - 构建工件: 您可以将二进制文件和其他构建工件上载到 GitLab并浏览和下载它们。 - Docker支持: 可以使用自定义Docker映像, 作为测试的一部分启动 服务, 构建新的Docker映像,甚至可以在Kubernetes上运行。 - 容器注册表: 内置的容器注册表, 用于存储,共享和使用容器映像。 - 受保护的变量: 在部署期间使用受每个环境保护的变量安全地存储和使用机密。 - 环境: 定义多个环境。三、Gitlab CI/CD架构 3.1Gitlab CI / CDGitLab的一部分,GitLab是一个Web应用程序,具有将其状态存储在数据库中的API。 除了GitLab的所有功能之外,它还管理项目/构建并提供一个不错的用户界面。3.2Gitlab Runner是一个处理构建的应用程序。 它可以单独部署,并通过API与GitLab CI / CD一起使用。3.3.gitlab-ci.yml定义流水线作业运行,位于应用项目根目录下 。为了运行测试,至少需要一个 GitLab 实例、一个 GitLab Runner、一个gitlab-ci文件四、Gitlab CI/CD工作原理- 将代码托管到Git存储库。 - 在项目根目录创建ci文件 .gitlab-ci.yml ,在文件中指定构建,测试和部署脚本。 - GitLab将检测到它并使用名为GitLab Runner的工具运行脚本。 - 脚本被分组为作业,它们共同组成了一个管道。管道状态也会由GitLab显示:最后,如果出现任何问题,可以轻松地 回滚所有更改:五、gitlab CI简介gitlab ci是在gitlab8.0之后自带的一个持续集成系统,中心思想是当每一次push到gitlab的时候,都会触发一次脚本执行,然后脚本的内容包括了测试、编译、部署等一系列自定义的内容。 gitlab ci的脚本执行,需要自定义安装对应的gitlab runner来执行,代码push之后,webhook检测到代码变化,就会触发gitlab ci,分配到各个runner来运行相应的脚本script。这些脚本有些是测试项目用的,有些是部署用的。六、Gitlab ci与Jenkins对比 6.1分支可配置性使用gitlab ci,新创建的分支无需任何进一步的配置即可立即使用CI管道中的已定义作业。 Jenkins基于gitlab的多分支流水线插件可以实现。相对配置来说,gitlab ci更加方便。6.2拉取请求支持如果很好的集成了存储库管理器的CI/CD平台,可以看到请求的当前构建状态。使用这个功能,可以避免将代码合并到不起作用或者无法正确构建的主分支中。 -Jenkins没有与源代码管理系统进一步集成,需要管理员自行写代码或者插件实现。 -gitlab与其CI平台紧密集成,可以方便查看每个打开和关闭拉动请求的运行和完成管道。6.3权限管理- gitlab ci是git存储库管理器gitlab的固定组件,因此在ci/cd流程和存储库直接提供了良好的交互。 - Jenkins与存储库管理器都是松散耦合的,因此在选择版本控制系统时它非常灵活。此外,就像其前身一样,Jenkins强调了对插件的支持,以进一步扩展或改善软件的现有功能。6.4插件管理扩展Jenkins的本机功能是通过插件完成的,插件的维护,保护和成本很高。 gitlab是开放式的,任何人都可以直接向代码库贡献更改,一旦合并,它将自动测试并维护每个更改七、Jenkins vs GitLab CI/CD 优缺点 7.1Jenkins 的优点- 大量插件库 - 自托管,例如对工作空间的完全控制 - 容易调试运行,由于对工作空间的绝对控制 - 容易搭建节点 - 容易部署代码 - 非常好的凭证管理 - 非常灵活多样的功能 - 支持不同的语言 - 非常直观7.2Jenkins 的缺点- 插件集成复杂 - 对于比较小的项目开销比较大,因为你需要自己搭建 - 缺少对整个 pipeline 跟踪的分析7.3GitLab CI/CD 的优点- 更好的 Docker 集成 - 运行程序扩展或收缩比较简单 - 阶段内的作业并行执行 - 有向无环图 pipeline 的机会 - 由于并发运行程序而非常易于扩展收缩 - 合并请求集成 - 容易添加作业 - 容易处理冲突问题 - 良好的安全和隐私政策7.4GitLab CI/CD 的缺点- 需要为每个作业定义构建并上传 / 下载 - 在实际合并发生之前测试合并状态是不可能的 - 还不支持细分阶段八、对比总结 8.1gitlab ci- 轻量级,不需要复杂的安装手段 - 配置简单,与gitlab可直接适配 - 实时构建日志十分清晰,UI交互体验很好 - 使用yaml进行配置,任何人都可以很方便的使用 - 没有统一的管理界面,无法统一管理所有的项目 - 配置依赖于代码仓库,耦合度没有Jenkins低8.2Jenkins- 编译服务和代码仓库分离,耦合度低 - 插件丰富,支持语言众多 - 有统一的web管理页面 - 插件以及自身安装较为复杂 - 体量较大,不适合小型团队开发。九、适用场景- gitlab ci有助于devops人员,例如敏捷开发中,开发人员与运维是同一个人,最便捷的开发方式 - Jenkins适合在多角色团队中,职责分明,配置与代码分离,插件丰富。
Gitlab CI/CD简介和jenkins对比 一、Gitlab CI/CD优势- 开源: CI/CD是开源GitLab社区版和专有GitLab企业版的一部分。 - 易于学习: 具有详细的入门文档。 - 无缝集成: GitLab CI / CD是GitLab的一部分,支持从计划到部署,具有出色的用户体验。 - 可扩展: 测试可以在单独的计算机上分布式运行,可以根据需要添加任意数量的计算机。 - 更快的结果: 每个构建可以拆分为多个作业,这些作业可以在多台计算机上并行运行。 - 针对交付进行了优化: 多个阶段,手动部署, 环境 和 变量。二、Gitlab CI/CD特点- 多平台: Unix,Windows,macOS和任何其他支持Go的平台上执行构建。 - 多语言: 构建脚本是命令行驱动的,并且可以与Java,PHP,Ruby,C和任何其他语言一起使用。 - 稳定构建: 构建在与GitLab不同的机器上运行。 - 并行构建: GitLab CI / CD在多台机器上拆分构建,以实现快速执行。 - 实时日志记录: 合并请求中的链接将您带到动态更新的当前构建日志。 - 灵活的管道: 您可以在每个阶段定义多个并行作业,并且可以 触发其他构建。 - 版本管道: 一个 .gitlab-ci.yml文件 包含您的测试,整个过程的步骤,使每个人都能贡献更改,并确保每个分支获得所需的管道。 - 自动缩放: 您可以 自动缩放构建机器,以确保立即处理您的构建并将成本降至最低。 - 构建工件: 您可以将二进制文件和其他构建工件上载到 GitLab并浏览和下载它们。 - Docker支持: 可以使用自定义Docker映像, 作为测试的一部分启动 服务, 构建新的Docker映像,甚至可以在Kubernetes上运行。 - 容器注册表: 内置的容器注册表, 用于存储,共享和使用容器映像。 - 受保护的变量: 在部署期间使用受每个环境保护的变量安全地存储和使用机密。 - 环境: 定义多个环境。三、Gitlab CI/CD架构 3.1Gitlab CI / CDGitLab的一部分,GitLab是一个Web应用程序,具有将其状态存储在数据库中的API。 除了GitLab的所有功能之外,它还管理项目/构建并提供一个不错的用户界面。3.2Gitlab Runner是一个处理构建的应用程序。 它可以单独部署,并通过API与GitLab CI / CD一起使用。3.3.gitlab-ci.yml定义流水线作业运行,位于应用项目根目录下 。为了运行测试,至少需要一个 GitLab 实例、一个 GitLab Runner、一个gitlab-ci文件四、Gitlab CI/CD工作原理- 将代码托管到Git存储库。 - 在项目根目录创建ci文件 .gitlab-ci.yml ,在文件中指定构建,测试和部署脚本。 - GitLab将检测到它并使用名为GitLab Runner的工具运行脚本。 - 脚本被分组为作业,它们共同组成了一个管道。管道状态也会由GitLab显示:最后,如果出现任何问题,可以轻松地 回滚所有更改:五、gitlab CI简介gitlab ci是在gitlab8.0之后自带的一个持续集成系统,中心思想是当每一次push到gitlab的时候,都会触发一次脚本执行,然后脚本的内容包括了测试、编译、部署等一系列自定义的内容。 gitlab ci的脚本执行,需要自定义安装对应的gitlab runner来执行,代码push之后,webhook检测到代码变化,就会触发gitlab ci,分配到各个runner来运行相应的脚本script。这些脚本有些是测试项目用的,有些是部署用的。六、Gitlab ci与Jenkins对比 6.1分支可配置性使用gitlab ci,新创建的分支无需任何进一步的配置即可立即使用CI管道中的已定义作业。 Jenkins基于gitlab的多分支流水线插件可以实现。相对配置来说,gitlab ci更加方便。6.2拉取请求支持如果很好的集成了存储库管理器的CI/CD平台,可以看到请求的当前构建状态。使用这个功能,可以避免将代码合并到不起作用或者无法正确构建的主分支中。 -Jenkins没有与源代码管理系统进一步集成,需要管理员自行写代码或者插件实现。 -gitlab与其CI平台紧密集成,可以方便查看每个打开和关闭拉动请求的运行和完成管道。6.3权限管理- gitlab ci是git存储库管理器gitlab的固定组件,因此在ci/cd流程和存储库直接提供了良好的交互。 - Jenkins与存储库管理器都是松散耦合的,因此在选择版本控制系统时它非常灵活。此外,就像其前身一样,Jenkins强调了对插件的支持,以进一步扩展或改善软件的现有功能。6.4插件管理扩展Jenkins的本机功能是通过插件完成的,插件的维护,保护和成本很高。 gitlab是开放式的,任何人都可以直接向代码库贡献更改,一旦合并,它将自动测试并维护每个更改七、Jenkins vs GitLab CI/CD 优缺点 7.1Jenkins 的优点- 大量插件库 - 自托管,例如对工作空间的完全控制 - 容易调试运行,由于对工作空间的绝对控制 - 容易搭建节点 - 容易部署代码 - 非常好的凭证管理 - 非常灵活多样的功能 - 支持不同的语言 - 非常直观7.2Jenkins 的缺点- 插件集成复杂 - 对于比较小的项目开销比较大,因为你需要自己搭建 - 缺少对整个 pipeline 跟踪的分析7.3GitLab CI/CD 的优点- 更好的 Docker 集成 - 运行程序扩展或收缩比较简单 - 阶段内的作业并行执行 - 有向无环图 pipeline 的机会 - 由于并发运行程序而非常易于扩展收缩 - 合并请求集成 - 容易添加作业 - 容易处理冲突问题 - 良好的安全和隐私政策7.4GitLab CI/CD 的缺点- 需要为每个作业定义构建并上传 / 下载 - 在实际合并发生之前测试合并状态是不可能的 - 还不支持细分阶段八、对比总结 8.1gitlab ci- 轻量级,不需要复杂的安装手段 - 配置简单,与gitlab可直接适配 - 实时构建日志十分清晰,UI交互体验很好 - 使用yaml进行配置,任何人都可以很方便的使用 - 没有统一的管理界面,无法统一管理所有的项目 - 配置依赖于代码仓库,耦合度没有Jenkins低8.2Jenkins- 编译服务和代码仓库分离,耦合度低 - 插件丰富,支持语言众多 - 有统一的web管理页面 - 插件以及自身安装较为复杂 - 体量较大,不适合小型团队开发。九、适用场景- gitlab ci有助于devops人员,例如敏捷开发中,开发人员与运维是同一个人,最便捷的开发方式 - Jenkins适合在多角色团队中,职责分明,配置与代码分离,插件丰富。