搜索到
154
篇与
的结果
-
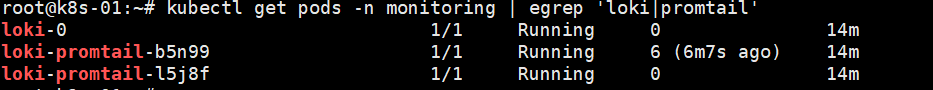
 loki 部署和镜像代理 一、部署 1.1 添加 Grafana 的 Helm 仓库helm repo add grafana https://grafana.github.io/helm-charts helm repo update1.2 安装 Loki Stack(只装 Loki + Promtail,不重复装 Prometheus/Grafana)#如果你有代理 临时生效 export http_proxy="http://192.168.3.135:7890" export https_proxy="http://192.168.3.135:7890" export HTTP_PROXY="$http_proxy" export HTTPS_PROXY="$https_proxy" # 内网和 k8s service 网段一般不走代理 export no_proxy="localhost,127.0.0.1,10.0.0.0/8,172.16.0.0/12,192.168.0.0/16,.svc,.cluster.local" export NO_PROXY="$no_proxy" #要全局永久生效,可以写到 /etc/environment 或 /etc/profile 里: sudo tee -a /etc/environment >/dev/null <<EOF HTTP_PROXY=http://192.168.3.135:7890 HTTPS_PROXY=http://192.168.3.135:7890 http_proxy=http://192.168.3.135:7890 https_proxy=http://192.168.3.135:7890 NO_PROXY=localhost,127.0.0.1,10.0.0.0/8,172.16.0.0/12,192.168.0.0/16,.svc,.cluster.local no_proxy=localhost,127.0.0.1,10.0.0.0/8,172.16.0.0/12,192.168.0.0/16,.svc,.cluster.local EOF #如果是docker运行时 每个节点都部署 其中 10.96.0.0/12 是很多 kubeadm 集群默认的 Service CIDR,可按你集群实际修改。 sudo mkdir -p /etc/systemd/system/docker.service.d sudo tee /etc/systemd/system/docker.service.d/http-proxy.conf >/dev/null <<EOF [Service] Environment="HTTP_PROXY=http://192.168.3.135:7890" Environment="HTTPS_PROXY=http://192.168.3.135:7890" Environment="NO_PROXY=localhost,127.0.0.1,10.96.0.0/12,10.0.0.0/8,172.16.0.0/12,192.168.0.0/16,.svc,.cluster.local" EOF sudo systemctl daemon-reload sudo systemctl restart docker sudo systemctl show --property=Environment docker #如果是containerd运行时 每个节点都部署 其中 10.96.0.0/12 是很多 kubeadm 集群默认的 Service CIDR,可按你集群实际修改。 sudo mkdir -p /etc/systemd/system/containerd.service.d sudo tee /etc/systemd/system/containerd.service.d/http-proxy.conf >/dev/null <<EOF [Service] Environment="HTTP_PROXY=http://192.168.3.135:7890" Environment="HTTPS_PROXY=http://192.168.3.135:7890" Environment="NO_PROXY=localhost,127.0.0.1,10.96.0.0/12,10.0.0.0/8,172.16.0.0/12,192.168.0.0/16,.svc,.cluster.local" EOF sudo systemctl daemon-reload sudo systemctl restart containerd sudo systemctl show --property=Environment containerd #创建pod helm install loki grafana/loki-stack \ -n monitoring --create-namespace \ --set grafana.enabled=false \ --set prometheus.enabled=false 二、配置 2.1 如果loki 和 prometheus在同一个名称空间下2.2 使用
loki 部署和镜像代理 一、部署 1.1 添加 Grafana 的 Helm 仓库helm repo add grafana https://grafana.github.io/helm-charts helm repo update1.2 安装 Loki Stack(只装 Loki + Promtail,不重复装 Prometheus/Grafana)#如果你有代理 临时生效 export http_proxy="http://192.168.3.135:7890" export https_proxy="http://192.168.3.135:7890" export HTTP_PROXY="$http_proxy" export HTTPS_PROXY="$https_proxy" # 内网和 k8s service 网段一般不走代理 export no_proxy="localhost,127.0.0.1,10.0.0.0/8,172.16.0.0/12,192.168.0.0/16,.svc,.cluster.local" export NO_PROXY="$no_proxy" #要全局永久生效,可以写到 /etc/environment 或 /etc/profile 里: sudo tee -a /etc/environment >/dev/null <<EOF HTTP_PROXY=http://192.168.3.135:7890 HTTPS_PROXY=http://192.168.3.135:7890 http_proxy=http://192.168.3.135:7890 https_proxy=http://192.168.3.135:7890 NO_PROXY=localhost,127.0.0.1,10.0.0.0/8,172.16.0.0/12,192.168.0.0/16,.svc,.cluster.local no_proxy=localhost,127.0.0.1,10.0.0.0/8,172.16.0.0/12,192.168.0.0/16,.svc,.cluster.local EOF #如果是docker运行时 每个节点都部署 其中 10.96.0.0/12 是很多 kubeadm 集群默认的 Service CIDR,可按你集群实际修改。 sudo mkdir -p /etc/systemd/system/docker.service.d sudo tee /etc/systemd/system/docker.service.d/http-proxy.conf >/dev/null <<EOF [Service] Environment="HTTP_PROXY=http://192.168.3.135:7890" Environment="HTTPS_PROXY=http://192.168.3.135:7890" Environment="NO_PROXY=localhost,127.0.0.1,10.96.0.0/12,10.0.0.0/8,172.16.0.0/12,192.168.0.0/16,.svc,.cluster.local" EOF sudo systemctl daemon-reload sudo systemctl restart docker sudo systemctl show --property=Environment docker #如果是containerd运行时 每个节点都部署 其中 10.96.0.0/12 是很多 kubeadm 集群默认的 Service CIDR,可按你集群实际修改。 sudo mkdir -p /etc/systemd/system/containerd.service.d sudo tee /etc/systemd/system/containerd.service.d/http-proxy.conf >/dev/null <<EOF [Service] Environment="HTTP_PROXY=http://192.168.3.135:7890" Environment="HTTPS_PROXY=http://192.168.3.135:7890" Environment="NO_PROXY=localhost,127.0.0.1,10.96.0.0/12,10.0.0.0/8,172.16.0.0/12,192.168.0.0/16,.svc,.cluster.local" EOF sudo systemctl daemon-reload sudo systemctl restart containerd sudo systemctl show --property=Environment containerd #创建pod helm install loki grafana/loki-stack \ -n monitoring --create-namespace \ --set grafana.enabled=false \ --set prometheus.enabled=false 二、配置 2.1 如果loki 和 prometheus在同一个名称空间下2.2 使用 -

-
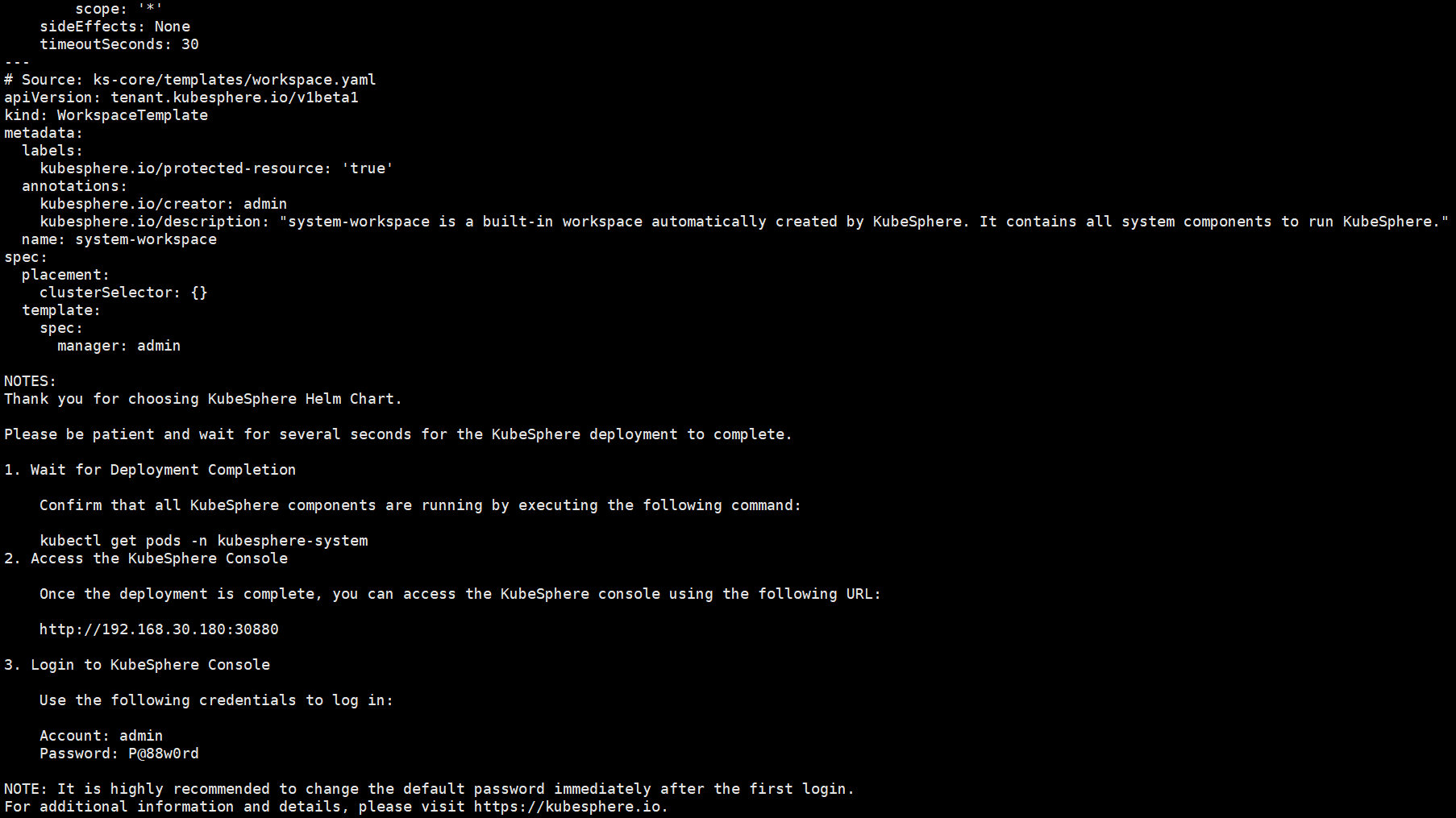
 KubeSphere部署 一、部署安装#官网 https://docs.kubesphere.com.cn/v4.2.0/01-intro/1.1 helmcurl -fsSL https://raw.githubusercontent.com/helm/helm/main/scripts/get-helm-3 | bash helm version1.2 安装 ks-corechart=oci://hub.kubesphere.com.cn/kse/ks-core version=1.2.2 helm upgrade --install \ -n kubesphere-system \ --create-namespace \ ks-core $chart \ --debug --wait \ --version $version \ --reset-values #拉取不到加这个 --set extension.imageRegistry=swr.cn-north-9.myhuaweicloud.com/ks1.3 查看安装结果kubectl get pods -n kubesphere-system1.4 访问http://192.168.30.180:30880 Account: admin Password: P@88w0rd二、激活 在web中拿到集群的ID然后去https://kubesphere.com.cn/apply-license/ 申请授权码 会发到邮箱中 然后在首页授权
KubeSphere部署 一、部署安装#官网 https://docs.kubesphere.com.cn/v4.2.0/01-intro/1.1 helmcurl -fsSL https://raw.githubusercontent.com/helm/helm/main/scripts/get-helm-3 | bash helm version1.2 安装 ks-corechart=oci://hub.kubesphere.com.cn/kse/ks-core version=1.2.2 helm upgrade --install \ -n kubesphere-system \ --create-namespace \ ks-core $chart \ --debug --wait \ --version $version \ --reset-values #拉取不到加这个 --set extension.imageRegistry=swr.cn-north-9.myhuaweicloud.com/ks1.3 查看安装结果kubectl get pods -n kubesphere-system1.4 访问http://192.168.30.180:30880 Account: admin Password: P@88w0rd二、激活 在web中拿到集群的ID然后去https://kubesphere.com.cn/apply-license/ 申请授权码 会发到邮箱中 然后在首页授权 -
 redis集群升级 总结升级redis 中间件的过程一、备份二、修改yal文件 更改镜像三、直接docker-compose up <容器的名字> 注意需要先升级slave再升级maste节点四、查看状态redis-cli -p 6001 -a <密码> info replication | egrep 'role|connected_slaves'root@37d65a2680e6:/data# redis-cli -c -p 6001 -a <密码> cluster info | egrep 'cluster_state|cluster_slots_ok|cluster_slots_fail'Warning: Using a password with '-a' or '-u' option on the command line interface may not be safe.cluster_state:okcluster_slots_ok:16384cluster_slots_fail:0
redis集群升级 总结升级redis 中间件的过程一、备份二、修改yal文件 更改镜像三、直接docker-compose up <容器的名字> 注意需要先升级slave再升级maste节点四、查看状态redis-cli -p 6001 -a <密码> info replication | egrep 'role|connected_slaves'root@37d65a2680e6:/data# redis-cli -c -p 6001 -a <密码> cluster info | egrep 'cluster_state|cluster_slots_ok|cluster_slots_fail'Warning: Using a password with '-a' or '-u' option on the command line interface may not be safe.cluster_state:okcluster_slots_ok:16384cluster_slots_fail:0 -
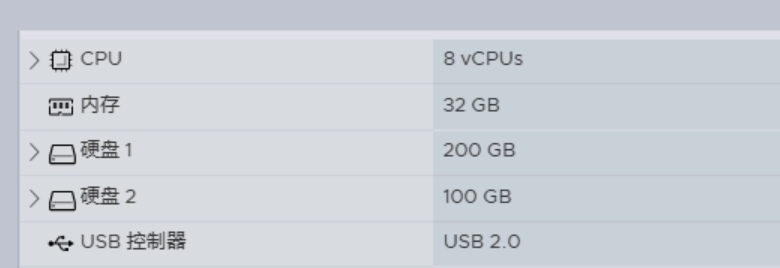
 esxi加硬盘 一、先给虚拟机加上硬盘 二、在虚拟机中识别 2.1 扫描SCSI总线以添加新设备在Linux系统中,尤其是虚拟化环境(如VMware, KVM, VirtualBox),新添加的SCSI硬盘可以通过触发系统重新扫描SCSI主机总线来识别。#首先,查看当前已连接的SCSI主机总线编号: ls /sys/class/scsi_host/#强制系统重新扫描所有的SCSI主机总线: echo "- - -" | sudo tee /sys/class/scsi_host/host*/scan#验证新硬盘是否被识别: lsblk2.2 加入扩容整个流程分为四步:创建物理卷 -> 扩展卷组 -> 扩展逻辑卷 -> 扩展文件系统。#将新磁盘 /dev/sdb 初始化为 LVM 物理卷 (PV) sudo pvcreate /dev/sdb #这条命令相当于告诉 LVM:“这块新磁盘交给你来管理”。 # Physical volume "/dev/sdb" successfully created.#将新的物理卷扩展到名为 rl的卷组 (VG) 中 sudo vgextend rl /dev/sdb #这条命令相当于把新来的“员工”(PV /dev/sdb)分配到了现有的“部门”(VG rl)里。现在这个部门就有了额外的100G“人力”(空间)。 #Volume group "rl" successfully extended#查看卷组确认空间,并扩展逻辑卷 (LV) sudo vgs # VSize(总大小) 变大了,并且 VFree(剩余空间) 这里显示了加入的 ~100G 空间。#方案A:将所有空闲空间都给 root sudo lvextend -l +100%FREE /dev/mapper/rl-root#方案B:只扩展指定大小(例如 50G) sudo lvextend -L +50G /dev/mapper/rl-root
esxi加硬盘 一、先给虚拟机加上硬盘 二、在虚拟机中识别 2.1 扫描SCSI总线以添加新设备在Linux系统中,尤其是虚拟化环境(如VMware, KVM, VirtualBox),新添加的SCSI硬盘可以通过触发系统重新扫描SCSI主机总线来识别。#首先,查看当前已连接的SCSI主机总线编号: ls /sys/class/scsi_host/#强制系统重新扫描所有的SCSI主机总线: echo "- - -" | sudo tee /sys/class/scsi_host/host*/scan#验证新硬盘是否被识别: lsblk2.2 加入扩容整个流程分为四步:创建物理卷 -> 扩展卷组 -> 扩展逻辑卷 -> 扩展文件系统。#将新磁盘 /dev/sdb 初始化为 LVM 物理卷 (PV) sudo pvcreate /dev/sdb #这条命令相当于告诉 LVM:“这块新磁盘交给你来管理”。 # Physical volume "/dev/sdb" successfully created.#将新的物理卷扩展到名为 rl的卷组 (VG) 中 sudo vgextend rl /dev/sdb #这条命令相当于把新来的“员工”(PV /dev/sdb)分配到了现有的“部门”(VG rl)里。现在这个部门就有了额外的100G“人力”(空间)。 #Volume group "rl" successfully extended#查看卷组确认空间,并扩展逻辑卷 (LV) sudo vgs # VSize(总大小) 变大了,并且 VFree(剩余空间) 这里显示了加入的 ~100G 空间。#方案A:将所有空闲空间都给 root sudo lvextend -l +100%FREE /dev/mapper/rl-root#方案B:只扩展指定大小(例如 50G) sudo lvextend -L +50G /dev/mapper/rl-root